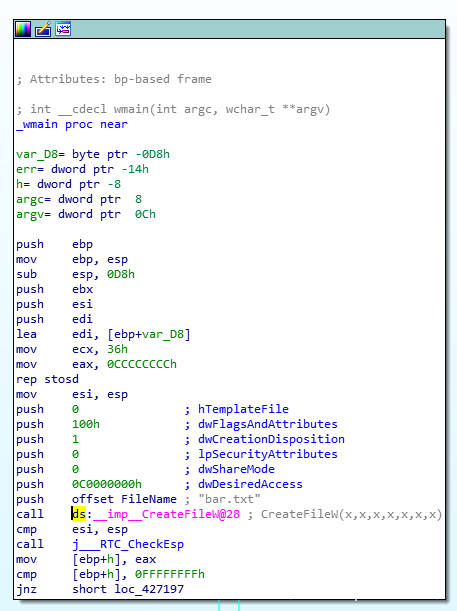
Intel CPU divides the privilege level into 4 levels: RING0, RING1, RING2, and RING3. Windows only uses two levels, RING0 and RING3. RING0 is only used by the operating system, and RING3 can be used by anyone. If an ordinary application attempts to execute the RING0 instruction, Windows will display an "illegal instruction" error message.
Challenge:
- Most modern CPUs do not support virtualization, such as x86
- Operating system privileged code that needs to directly access memory and hardware must be executed in Ring 0
- CPU virtualization must add VMM (Ring 0) under Guest OS
- Some key instructions have different semantics when executed at the non-Ring 0 permission level: they cannot be effectively virtualized, such as POPF instructions
- Non-privileged instructions can query the current privilege level of the CPU, and x86 does not trap these instructions
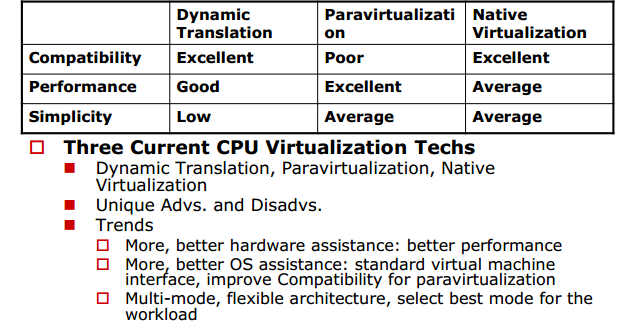
CPU Virtualization Tech
Full Virtulization
Introduction: It is mainly to capture and process those privileged instructions that are sensitive to virtualization between the guest operating system and the hardware, so that the guest operating system can run without modification. The speed will vary according to different implementations, but it can roughly meet the needs of users . This method is the most mature and common in the industry today, and it belongs to both the Hosted mode and the Hypervisor mode. Well-known products include IBM CP/CMS, VirtualBox, KVM, VMware Workstation and VMware ESX (it is in its 4.0 version, which is Renamed to VMware vSphere).
Advantages: Guest OS does not need to be modified, speed and functions are very good, and more importantly, it is very simple to use, whether it is a VMware product or a Sun (Oracle?) VirtualBox.
Disadvantages: The performance of fully virtual products based on the Hosted model is not particularly excellent, especially in terms of I/O.
Future: Because of the use of this model, not only will the Guest OS be exempt from modification, but also the performance will be improved by introducing hardware-assisted virtualization technology. I personally judge that full virtualization is still the mainstream in the future.
Paravirtualization (Parairtulization)
Introduction: It is somewhat similar to full virtualization. It also uses Hypervisor to achieve shared access to the underlying hardware. However, because the Guest OS running on the Hypervisor has integrated code related to paravirtualization, the Guest OS can perform very well. Cooperate with Hyperivosr to realize virtualization. In this way, there is no need to recompile or capture privileged instructions, so that its performance is very close to that of a physical machine. Its most classic product is Xen, and because Microsoft's Hyper-V uses a technology similar to Xen, Hyper-V can also be used Belongs to paravirtualization.
Advantages: Compared with full virtualization, this model has a more streamlined architecture and has certain advantages in overall speed.
Disadvantages: Need to modify the Guest OS, so it is more troublesome in terms of user experience.
Future: I think it should be similar to the current situation in the future. It should continue to occupy a place on the public cloud (such as Amazon EC2) platform, but it is difficult to compete with fully virtualized products like VMware vSphere in other aspects. Will use hardware-assisted virtualization technology to increase speed and simplify the architecture.
Hardware Assisted Virtualization (Hardware Assisted Virtualization)
Introduction: Intel/AMD and other hardware manufacturers improve performance by hardwareizing some of the software technologies used in full virtualization and paravirtualization (the details will be detailed below). Hardware-assisted virtualization technology is often used to optimize full-virtualization and para-virtualization products, rather than being original. The most famous example is VMware Workstation. Although it belongs to full virtualization, hardware-assisted virtualization was introduced in its 6.0 version. Technology, such as Intel’s VT-x and AMD’s AMD-V. The mainstream full virtualization and paravirtualization products on the market now support hardware-assisted virtualization, including VirtualBox, KVM, VMware ESX and Xen.
Advantages: By introducing hardware technology, virtualization technology will be closer to the speed of physical machines.
Disadvantages: The existing hardware implementation is not optimized enough, and there is room for further improvement.
Future: Because the use of hardware technology can not only increase speed, but also simplify the architecture of virtualization technology, it is foreseen that hardware technology will be adopted by most virtualization products.
Operating System Level Virtualization (Operating System Level Virtualization)
Introduction: This technology realizes virtualization by simply isolating the server operating system, and is mainly used for VPS. The main technologies include Parallels Virtuozzo Containers, chroot on Unix-like systems and Zone on Solaris.
Advantages: Because it is a direct modification of the operating system, the implementation cost is low and the performance is good.
Disadvantages: poor performance in resource isolation, and there are restrictions on the model and version of the Guest OS.
Future: Unclear, I think unless revolutionary technology is born, it should belong to the minority, such as VPS.