Using iptables to prevent syn flood attacks
command:
iptables -N syn-flood
iptables -A syn-flood -m limit --limit 50/s --limit-burst 10 -j RETURN
iptables -A syn-flood -j DROP
iptables -I INPUT -j syn-flood
Explanation:
-NCreate a new chain
--limit 50/sMeans 50 times per second; 1/m is once per minute
--limit-burstThe maximum number of packages allowed to trigger the limit limit (default 5), it is like a container, with a maximum of 10, and more than 10 will not fit, these packages will be given to the following rules
-I INPUT -j syn-floodSubmit the INPUT packet to the syn-flood chain for processing
Here --limit-burst=10 is equivalent to saying that there are 10 matching packets to forward at the beginning, and then the number of matched packets is limited according to --limit=50/s, which is to limit forwarding per second The 50 data packets, the excess will be processed by the following DROP rules that meet the requirements and discarded, so that the speed limit of the data packet is realized.
Expansion:<Content from "Cloud Computing Network Zhuji">
Intelligent Recommendation
[DDOS] Clever use iptables to get a SYN flood attack!
SYN Flood (SYN Flood) is a typical DoS (Denial of Service) attack and is a type of DDoS attack. After the attack, the server TCP connection resource is exhausted, and finally stops responding to the n...
Clever use of iptables five tricks to get SYN flood attack for free
Reprinted source: Use iptables five tricks to get SYN flood attack for free: https://www.toutiao.com/i6772397997692027399/ Abstract: SYN Flood is a typical DoS attack, which is a kind of DDos attack. ...
Syn flood program in python using raw sockets (...
2019 Unicorn Enterprise Heavy Recruitment Python Engineer Standard >>> Transferred fromhttp://www.binarytides.com/syn-flood-program-in-python-using-raw-sockets-linux/ Syn flood and raw socket...
syn flood
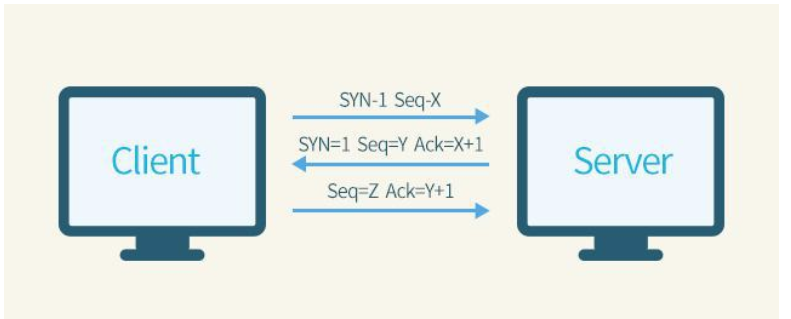
In the process via a tcp, client side and the server side even in the building, client side to the server first sends a packet to tcp syn the flag. Like when we first asked qq chat, without beauty? Af...
Modern computer network experiment of SYN flood attacks and SYN cookie Principle Analysis
Environment (detailed instructions for configuring experiments running operating system, network platform, the machine) The host operating system WIN10 Open source virtual machine management software ...
More Recommendation
Shell+Iptables defends against TCP SYN flooding attacks
In the operation and maintenance of a certain platform, a very large number of access cards are found in the SYN_RECV state, which can be confirmed as a SYN flood attack. The netstat -antp state seen ...
TCP SYN-Flood attack
This article is reproduced fromHuawei Enterprise Interactive Community Hello everyone, Strong Uncle and you have met again! The last period of the uncle, with everyone to understandBasic defense knowl...
DDoS -- syn flood
1 Overview The SYN flood is one of the Network layer's DDoS attacks. This attack exploits the TCP handshake defect to consume the resources of the attacked party and causes the attacked party to refus...
SYN flood attack (forwarding)
SYN flood attack Transfer from the principle, prevention and elimination of SYN flood attack SYN flood attack overview The SYN flooding attack uses the shortcoming of the TCP three-way handshake proto...
syn flood(sylixos)
SYN FLOOD flood attack: ...