Python parses the pcap data packet, and then exports to csv file
Because network topology discovery and operating system identification are achieved by wireshark capturing communication packets on the network, I want to parse the pcap data packets captured by wireshark and extract the network characteristics and specific values, and It is saved in csv format. One afternoon, finally let me understand the principle.
1. Use the SCAPY module to parse pcap packets
First, make sure that the scapy library is installed in python. If not, use: pip install scapy to install
Secondly, when calling the scapy module, you must use from scapy.all import * to call it correctly.
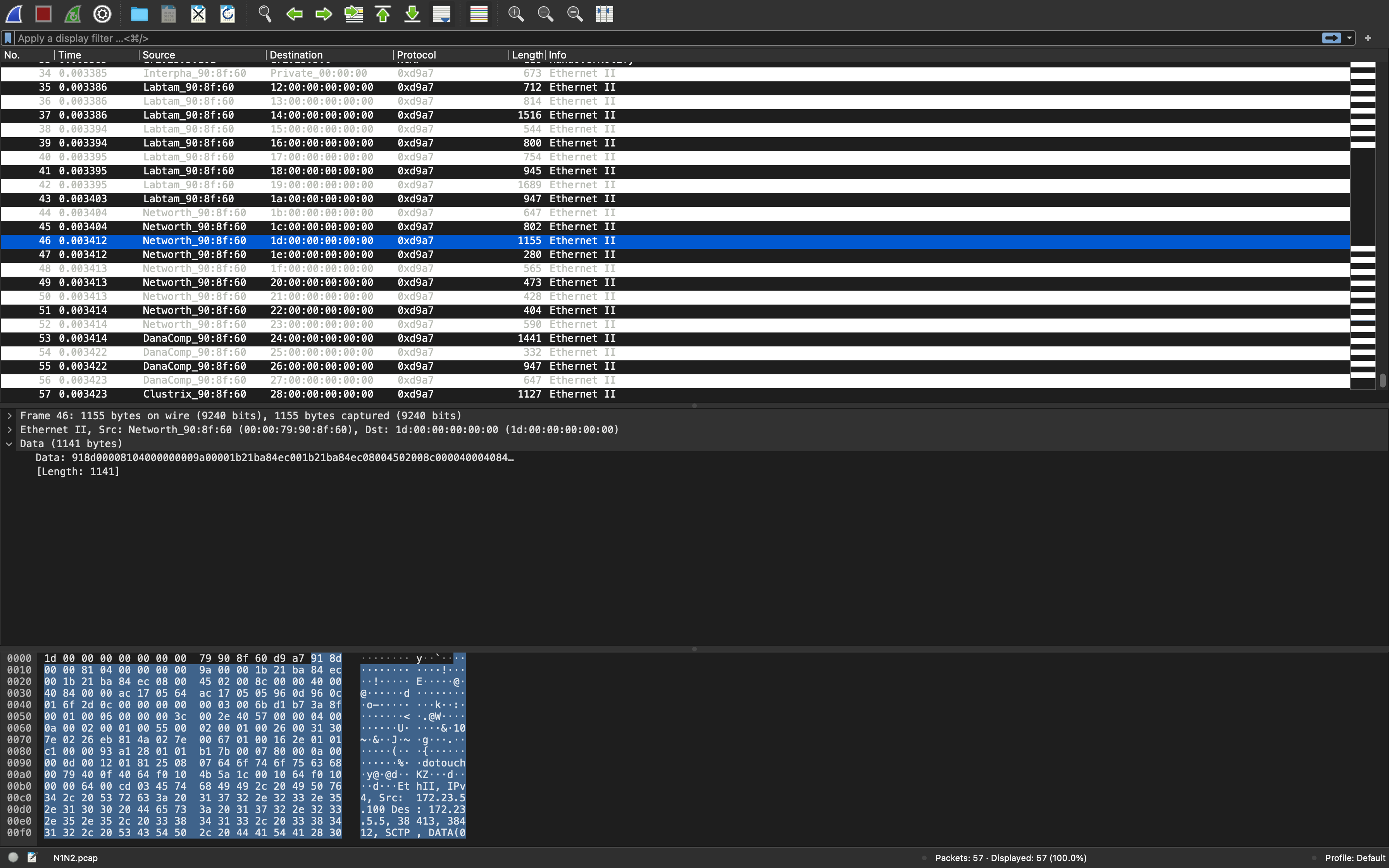
After reading it, we know that when scapy reads a pcap file, it actually reads a list, which can be debugged by the cmd-python command, as shown in the following figure:

We can see from the picture, because the pcap package contains many data packets, so the pkts read in represent all the data contained in the pcap package, and pkts[i] means in pcap The i-th data in the example in the figure is: I saved the filtered data packet containing only the TCP protocol in wireshark, so what I got is a data packet containing a TCP protocol, if you want to know each packet The specific format can be displayed through the show() function. To extract the value of a specific network attribute in each packet, use pkts[i][
Fields of the corresponding structure—TCP correspondence: ‘Ethernet’, ‘IPv6’, ‘TCP’]. Specific attribute names are shown in the following code:
from scapy.all import *
pkts = rdpcap("tcp02.pcap")
pkt0=pkt[0]
dst=pkt0['Ethernet'].dst
version = pkt0['IPv6'].version
sport = pkt0['TCP'].sport
2. Import the data in the pcap package into the csv file
The following is the extraction of the network characteristics of a data packet, the code is as follows:
import csv
from scapy.all import *
pkts = rdpcap("tcp02.pcap")
pkt0 =pkts[0]
headers=['dst','src','type','version','tc','f1','plen','nh','hlim','IPsrc','IPdst','sport','dport','seq','ack',
'dataofs','reserved','flags','window','chksum','urgptr','optionsmss','optionsNOP0','optionsWScale',
'optionsNOP1','optionsNOP2','optionsSAckOK']
a1=pkt0['Ethernet'].dst
a2=pkt0['Ethernet'].src
a3=pkt0['Ethernet'].type
b1=pkt0['IPv6'].version
b2=pkt0['IPv6'].tc
b3=pkt0['IPv6'].fl
b4=pkt0['IPv6'].plen
b5=pkt0['IPv6'].nh
b6=pkt0['IPv6'].hlim
b7=pkt0['IPv6'].src
b8=pkt0['IPv6'].dst
c1=pkt0['TCP'].sport
c2=pkt0['TCP'].dport
c3=pkt0['TCP'].seq
c4=pkt0['TCP'].ack
c5=pkt0['TCP'].dataofs
c6=pkt0['TCP'].reserved
c7=pkt0['TCP'].flags
c8=pkt0['TCP'].window
c9=pkt0['TCP'].chksum
c10=pkt0['TCP'].urgptr
c11=pkt0['TCP'].options[0][1]
c12=pkt0['TCP'].options[1][1]
c13=pkt0['TCP'].options[2][1]
c14=pkt0['TCP'].options[3][1]
c15=pkt0['TCP'].options[4][1]
c16=pkt0['TCP'].options[5][1]
rows=[a1,a2,a3,b1,b2,b3,b4,b5,b6,b7,b8,c1,c2,c3,c4,c5,c6,c7,c8,c9,c10,c11,c12,c13,c14,c15,c16]
with open('test3.csv','w',newline ='') as f:
fcsv= csv.writer(f)
fcsv.writerow(headers)
fcsv.writerow(rows)
Intelligent Recommendation
Share a small python program that extracts the packet timestamp in the pcap file
As the title, share a small program to extract the timestamp in python. ...
Pcap file from the packet analysis
Use dpkt library...
Python extracts the original data in the pcap file
In the project, the data needs to be checked according to the original data in the pcap file, and it is too inconvenient to use wireshark to view So I hope to extract all the packets in the file and a...
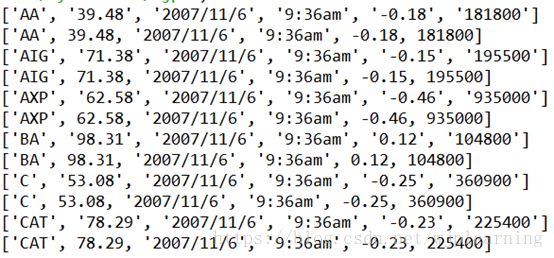
Python reads CSV and parses json format data
1 read and write CSV file Raw CSV file data Figure 1: Stock data stocks.csv 2 read the stock data as a tuple sequence Code: import csv with open('stocks.csv') as f: f_csv = csv.read...
JS exports Datatable table data to CSV file
Requirement: Export the webpage datatable to an Excel spreadsheet, which is required to be a CSV format file. The export button click event is as follows: ...
More Recommendation
Js exports json data to csv file
First pit...
Hbase exports data into csv format or flat file
background Recently, business departments need to export Hbase data into csv format files or flat files (flat format). The difficulty encountered is that there is no fixed column name in Hbase. Langua...
Oracle exports data to CSV file -OK
In the work, there is a need to export online data to Excel to analyze/view the customer. As follows, the method introduces: UTL_FILE read and write file package, the amount of data exported in 1 minu...