4. Network layer: Layer 3 physical equipment: hubs, switches, routers [IP, ICMP, BGP, OSPF
tags: Network protocol
4. Network layer: Layer 3 physical equipment: hubs, switches, routers [IP, ICMP, BGP, OSPF
- 1. Hub (the device on the first floor, just use it directly without changing anything)
- 2. Link layer switch (Layer 2 device, modify the mac header. Unlock the mac header and operate according to the ip header. For example, ARP operates through the ip information, and then forwards according to the mac header. Also called the second layer packet switch, Because two layers will be used)
- 3. Router (Layer 3 device, modify mac header and ip header. Unlock mac and ip and see what's inside. Layer 3 is used)
- 4. Packet switch: all-rounder, universal forwarding
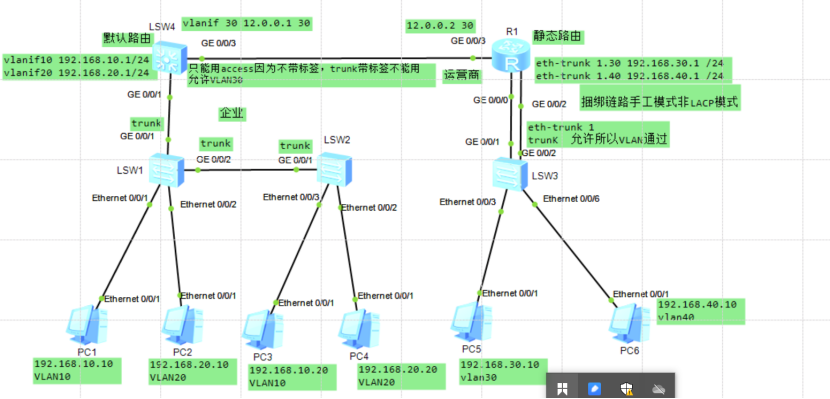
When a data packet is sent from the client, it will pass through many physical devices to finally find the server. The following describes various servers.
The switch is a packet switch on the second layer, and the router is a packet switch on the third layer.
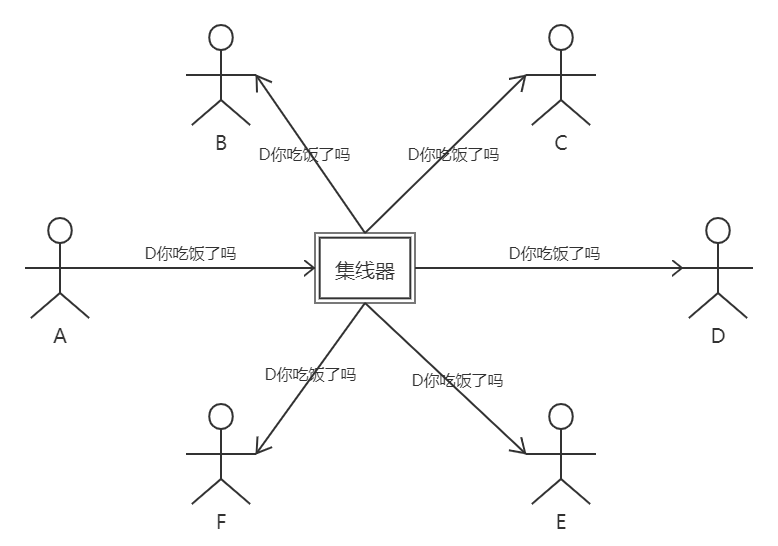
1. Hub (the device on the first floor, just use it directly without changing anything)
The hub works at the physical layer. It uses a broadcast method to copy every byte it receives to all other ports, that is, the data packet sent by the client can be seen by everyone.
Problems with hubs: security (the package can be seen by everyone), bandwidth
2. Link layer switch (Layer 2 device, modify the mac header. Unlock the mac header and operate according to the ip header. For example, ARP operates through the ip information, and then forwards according to the mac header. Also called the second layer packet switch, Because two layers will be used)
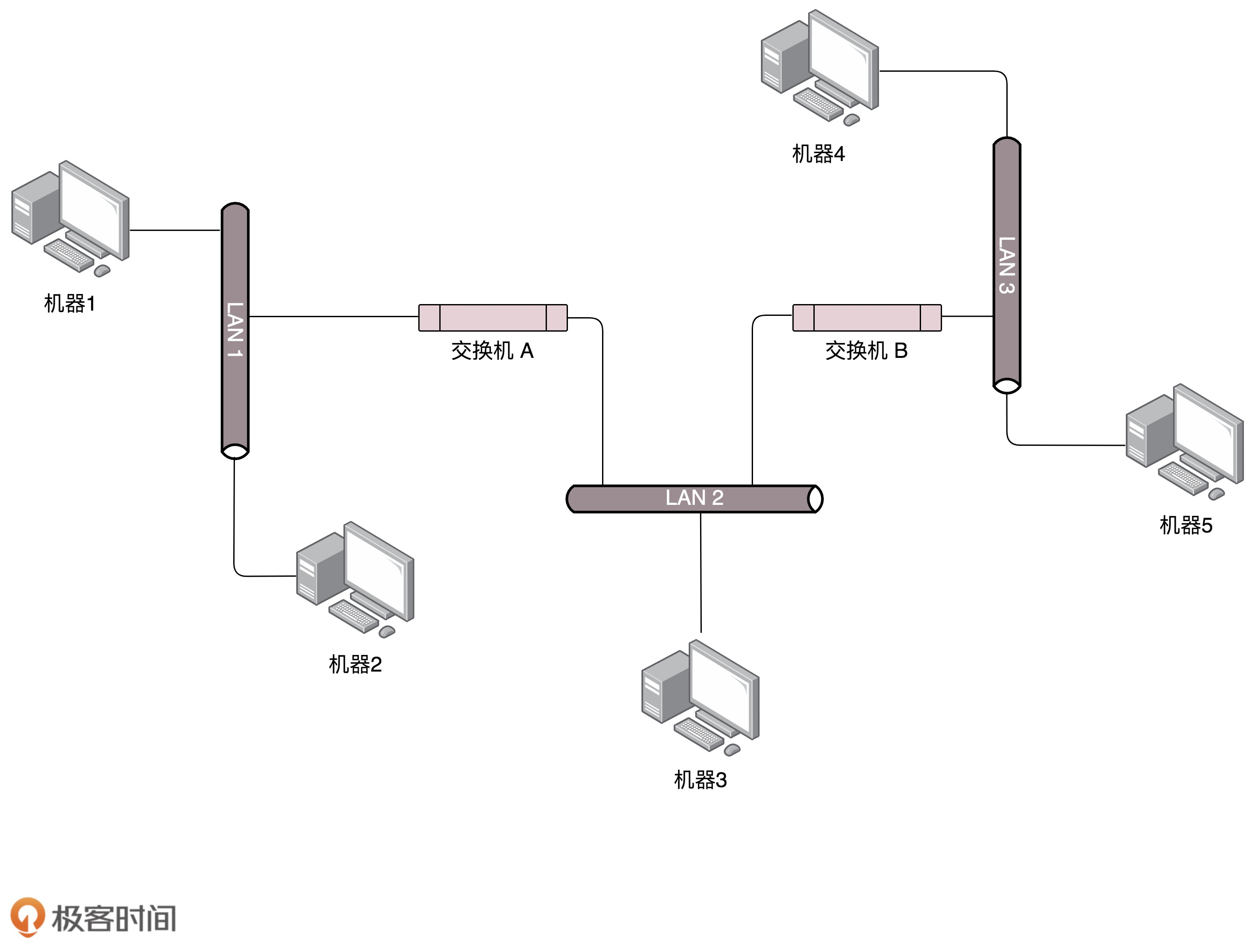
The switch will learn and learn the correspondence between the mac address of each device and the forwarding port on the switch, and the data packets sent to the mac will only be sent to this port. The information learned by the switch will be recorded in the forwarding table.
ARP request process:
There is no information in the forwarding table of the switch at the beginning. Machine 1 only knows the IP address of machine 4 and initiates a broadcast. Switch A also broadcasts because it does not know where machine 4 is. Broadcast to switch B continuously for broadcasting. After receiving the broadcast, machine 4 will respond and reply with the MAC information, and the information will be sent back to machine 1 through broadcast, and machine 1 will know the mac address of machine 4. During this process, both switch A and switch B know the corresponding ports of machine 1 and machine 4 respectively. If you find machine 1 next time, it will not broadcast, just send it to the learned port.
A graph topology is formed between the switch and the host and other devices. Such a simple switch has loop problems. The same information may return to the switch from multiple ports in a circle, and the switch does not know where the machine is. Since it is a graph, solving the loop problem can be solved by the minimum spanning tree algorithm STP (this belongs to the spanning tree of the undirected graph with power).
The problem with the switch: security (the packet can still be seen by many people, because the forwarding table will occasionally be updated, and then it will still be broadcast)
Solution:
Physical isolation: divided into separate switches and configured with separate subnets. The switch is no longer directly connected to the switch, but is connected through a router. In this way, there is no situation where the information of a switch is heard by a switch that should not be heard. But this requires a lot of switches, which is easy to cause waste of switch interfaces.
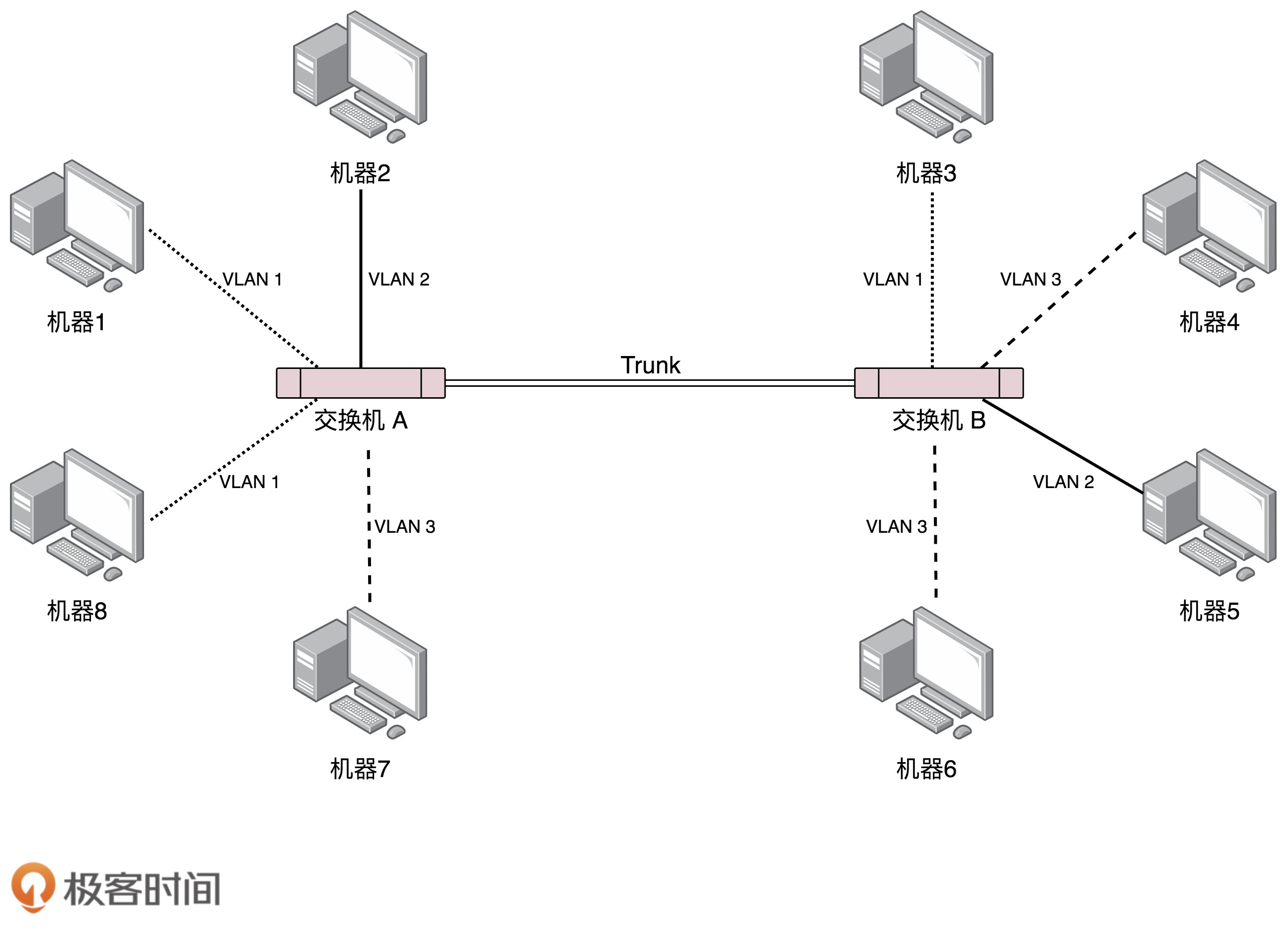
Virtual isolation: VLAN virtual local area network is used, so that a switch will be connected to machines belonging to multiple LANs.
Only packets of the same VLAN will be forwarded to each other, and packets of different VLANs will not be seen. Similar to adding a piece of LAN information as a judgment before broadcasting, only the same LAN is broadcast.
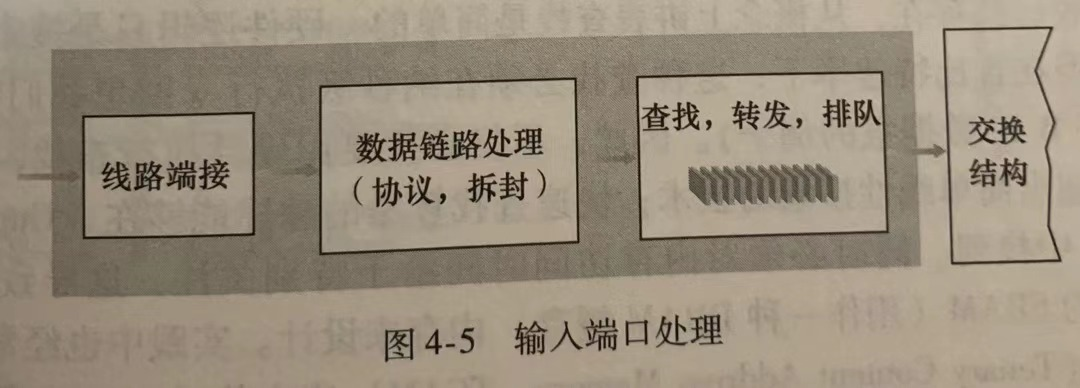
3. Router (Layer 3 device, modify mac header and ip header. Unlock mac and ip and see what's inside. Layer 3 is used)
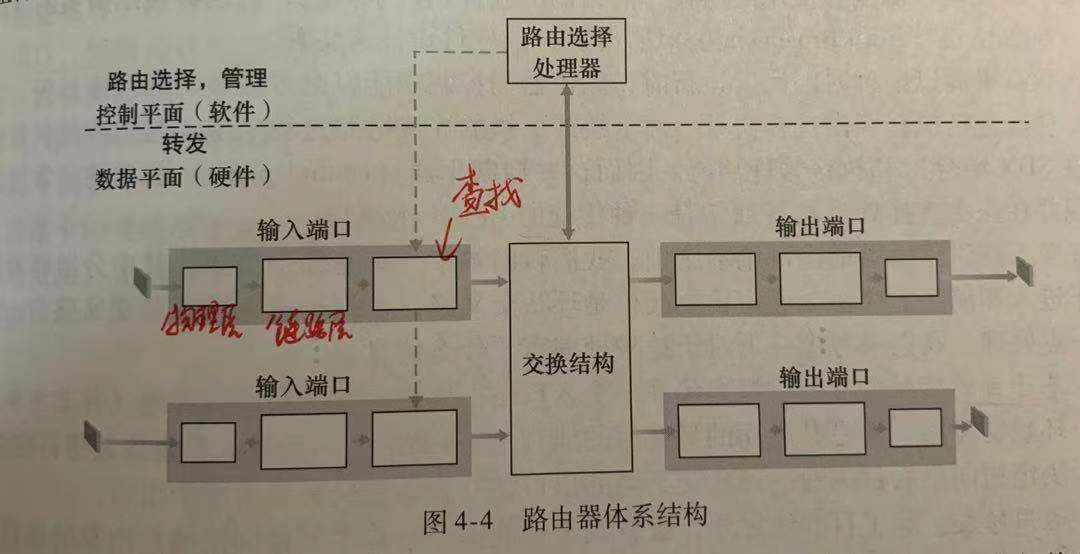
(1) The gateway is often a router, but the router is not just a gateway. The router has multiple network ports or network cards, and then multiple LANs. For each LAN, the router is a gateway. If the route knows to go to a certain destination (IP address), where is the next stop (the IP of the next gateway) that it needs to go to, which is constantly updated.
The gateway is equivalent to the customs. It can be said that this is the border from the mainland to Hong Kong, or it can be said to be the border from Hong Kong to the mainland.
When the data packet exits the LAN through the gateway, the mac header should be replaced (because this mac header only means that I will go to this gateway in the next stop. Now I have reached the gateway and I am going to the next stop. Naturally, I need to change the mac of the next stop The final destination is recorded by the IP, and the MAC records the next destination. However, the MAC address of the final destination cannot be directly used as the initial destination address. The reason is simple, because you don’t know the destination address at all. , Isn’t the purpose of my trip just to know about this. So similar to IP recording long-term goals, mac recording short-term goals, step by step closer to the end.). In the message, each header stores different information and records the protocol used by the next layer. For example, the MAC records that the next layer uses the IP protocol instead of the ICMP protocol, and the IP header records the use of the next layer. Is it TCP or IP protocol.
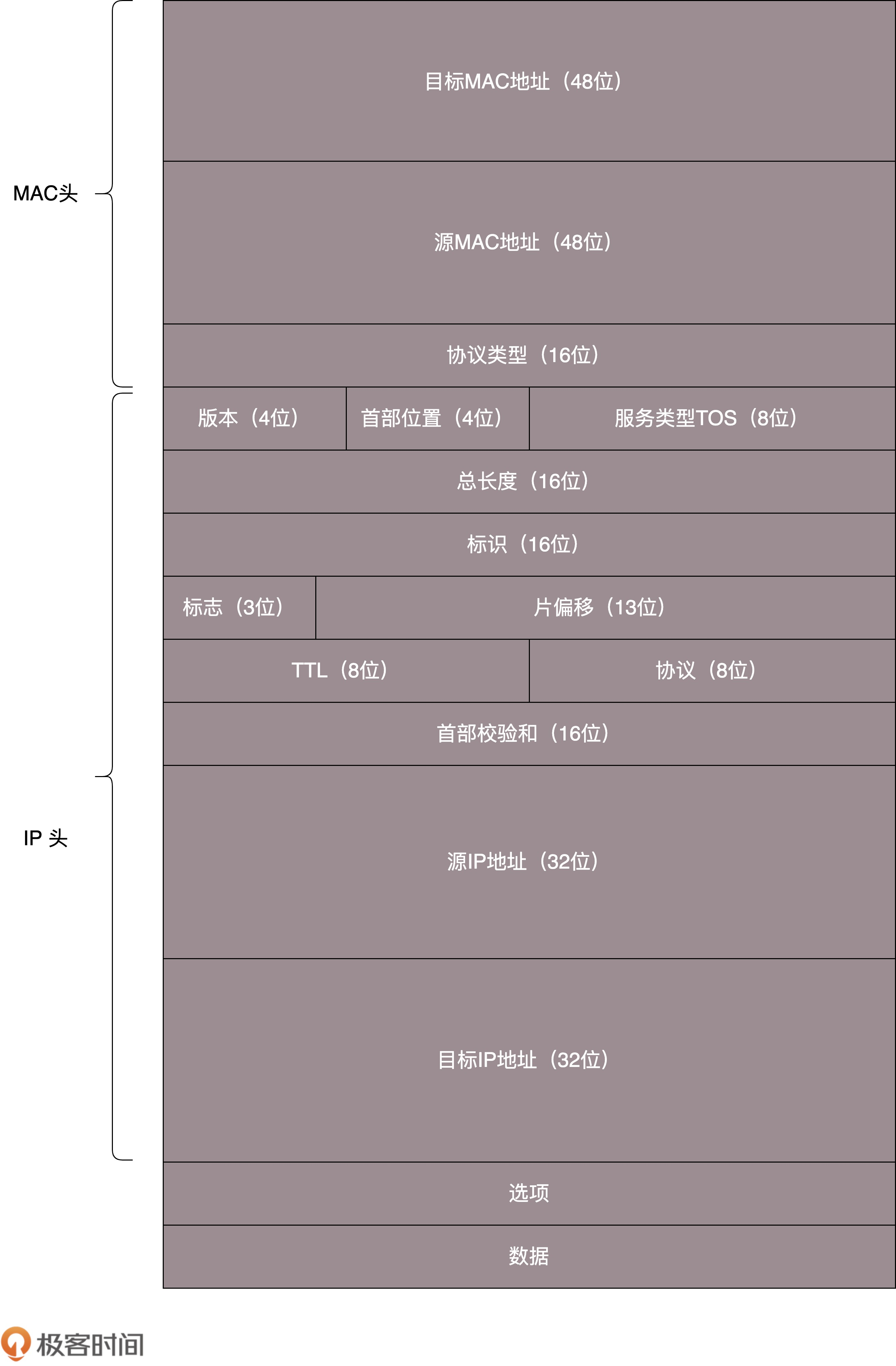
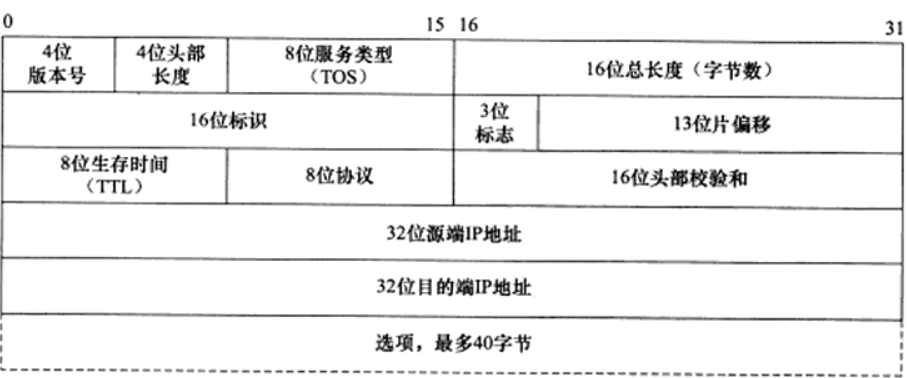
IPv4 packet
[TTL: Time to live, life span, to ensure that datagrams will not loop indefinitely. Decrease by one every time a route is passed, and discard when it reaches 0.
[Why both IP and TCP perform error detection? On the one hand, the checksum of IP only checks the header, and the checksum of TCP checks the entire datagram. Secondly, TCP and IP are not necessarily used together. TCP can be used with other network layer protocols, and IP can also be used with other transport layer protocols.
[Identification, flag, and fragment offset are used to assemble fragmented IPv4 packets. Because the link layer protocol used on the path of the sender and the destination is not necessarily the same, and their MTU (Maximum Transmission Unit) is not necessarily the same, so some data packets may be fragmented into multiple Data packet, and then write the information in the header, let the end system assemble.
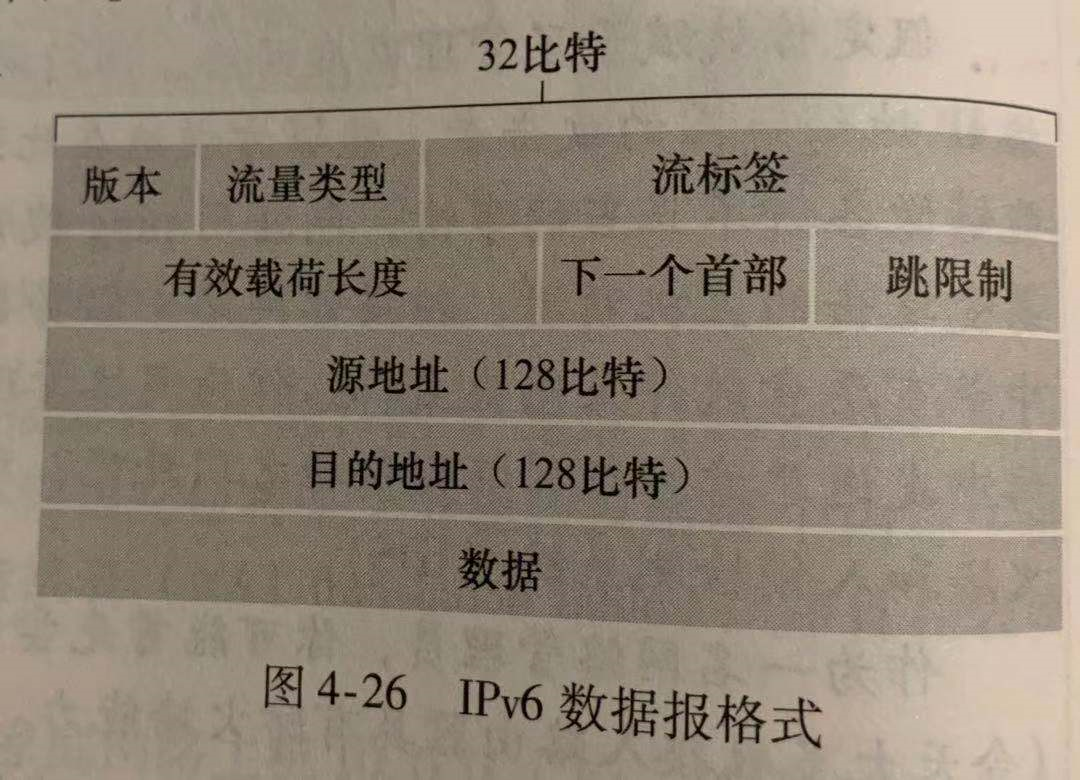
IPv6 packet
IPv6 does not have identification, flag, and fragment offset, because IPv6 does not allow fragmentation and reassembly (because these two operations are too time-consuming), if the data packet is found to be too large on the road, it will be directly discarded, and then a "packet" will be returned. Too big" ICMP error message.
IPv6 does not have the first checksum, because it feels time-consuming, just leave it to the transport layer protocol to do it.
How to migrate between IPv4 and IPv6? With tunnels, if the head and tail routers use IPv6 protocol and IPv4 is used in the middle, then when the IPv4 router is reached, the entire IPv6 data is packed into the IPv4 payload field (the header is also inserted), and the IPv6 is used. Route where it is taking it out. Similar to hitchhiking with dolls.
(2) Static routing
It is to configure rules one by one on the router. Those who meet condition A go to port 1 to the No. 1 LAN, and those who meet condition B go to port 2 to the No. 2 LAN. Here the gateway is divided into forwarding gateway (not changing the IP address, only changing the MAC header) and NAT gateway (changing both the IP address and the MAC header). The satisfaction condition mentioned here is generally to match the first N digits of the IP and use the longest prefix matching rule for forwarding.
One, forwarding gateway
Every station does not change the IP. Whenever you arrive at a gateway, you will see where the destination IP is, and then point out the IP of the next gateway based on the static routing information, get the mac of the next gateway through ARP, change the mac header The packet is passed to the next gateway and repeated continuously. Until the last gateway, I found that I and the destination ip are in the same local area network, then directly broadcast ARP to get the destination mac and arrive.
2. NAT gateway (Network Address Translation): vest
The IP address of the receiver and the sender may be the same. The mac is the only one in the world, but the IP is not necessarily. Just like the gateway IP of the house is 192.168.0.1, it means that we use the 192.168.0 field at home ip. It is easy to conflict. The sender and receiver appear to be in the same local area network, but they are not actually (that is, public network and private network). The solution to this problem is the NAT gateway.
To put it simply, the ip of the sender and the receiver can be repeated, but the ip of the gateway is not repeated. Then when the receiver sends the packet, the destination address is filled with the ip of the gateway where the destination is located. When going out of the LAN, the gateway will change the sender's ip address, which is equivalent to putting on a vest and replacing it with the gateway's ip. It is equivalent to a spokesperson. Everyone is shouting by younger brothers and sisters at home, but when they have a blind date with others, they will be the parents. Wang’s daughter wanted to chat with Zhang’s parents, so she got rid of the head of the Wang family. The head of the Wang family requested to talk to the head of the Zhang family. The whole process said that we were talking between the heads of the family. In fact, it was passed to the last Zhang family. The head will switch back to ip, find the eldest son in the local area network, and relay the words. Because all daughters have eldest sons in their families, but the head of the Wang family and the head of the Zhang family are unique. The daughter of the Wang family cannot say, I want to find a son to chat, and every family has a son. Who knows that she is looking for Zhang family.
The specific implementation is to use the subnet to send the data packet to the NAT gateway, the gateway will record the subnet IP address and source port number of the source data packet (such as 3345), and then rewrite the IP and port number (such as 5001), and then translate it in the NAT The added entry record 5001 in the table corresponds to port 3004 and the IP address of the subnet. In this way, all packets sent to this gateway's masqueraded IP with port 5001 can be correctly forwarded to the source address.
(3) Dynamic routing algorithm
The dynamic routing table is generated according to the routing protocol algorithm, and it changes with the change of the network operation status, which is the shortest path problem of finding the map.
[1] Distance vector routing algorithm (Distance-Vector, DV algorithm): Based on Bellman-Ford algorithm: Keep an eye on long-term goals, everyone pays attention to the distance to the destination
A table is stored in each route. The shortest distance from A to B is a1, the shortest distance from A to C is a2, the shortest distance from A to D is a3, the shortest distance from B to C is b1, and so on. That is, what is recorded is the shortest distance from each router to other routers, that is, one distance vector. If a router finds that the distance between itself and its neighbor has changed, it will notify the neighbor. When the neighbor receives the change, it checks and updates its routing table. Some paths may have better choices. Then the updated entries will be notified to the corresponding neighbors. In this way, it stays still when no update message is sent at the end until a new change occurs. In DV, each route only communicates with its neighbors, but provides the neighbor with the lowest cost estimate from itself to all routers.
Advantages: low link overhead
Disadvantages: slow convergence and spread far away if the route is wrong
[2] Link State broadcast (LS algorithm): Based on the Dijkstra algorithm: as a small group, everyone pays attention to the distance to the neighbor first
Each route knows the cost of all nodes, namely A to B, A to C, [Because A is not directly connected to D, there is no information from A to D, which is different from the distance vector].
Each router keeps global information, knows the distance between each router and the destination, and the next router it should go to. The router updates its distance from the destination according to the distance between its neighbor and the destination and the distance from its neighbor.
The disadvantage of this method is that it takes a long time for everyone to find out when the route goes offline. At the same time, the entire global routing table must be sent every time a message is sent. In LS, each route communicates with all routes, but only provides its own cost to neighbors.
Advantages: fast convergence, routing calculation is separated, everyone calculates separately, so it is more robust
Disadvantages: high link overhead
Specific agreement:
[1] OSPF (Open Shortest Path First, Open Shortest Path First) based on link state routing algorithm
Mainly used inside the data center, called the Interior Gateway Protocol (IGP), to find the shortest path within the organization.
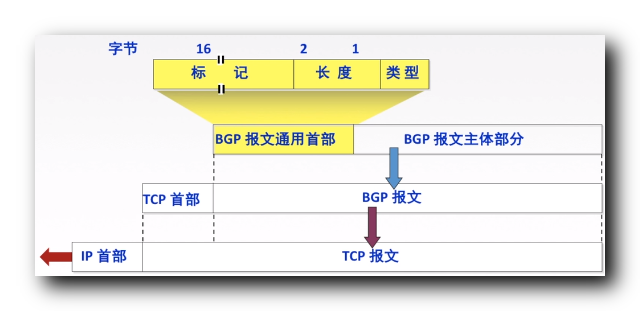
[2] BGP (Border Gateway Protocol, BGP for short) based on distance vector routing algorithm
Also called AS (Autonomous System) routing protocol. Mainly used in the external network, it allows each subnet to advertise its existence to other parts of the Internet. If there is no BGP, each subnet is an island.
The border routers of the autonomous system use eBGP to broadcast, and the routing information learned by border routing is transmitted to the intranet using iBGP, so that the intranet knows which border route is best to route from. For example, the border routes of the three ASs are AS1a, AS2a, and AS3a. 10 is the internal route or host in AS1. When AS1a-0 sends data packets, the AS1a border router will write its own name "AS1a 10" in front, which means that through AS1a I can find my 10 hosts. Then when the data packet passes through AS2a, AS2a can put its own name "AS2a AS1a 10" so that everyone can know that there is 10 and how to get there.
The disadvantage of distance vector routing protocol is slow convergence, but BGP regards an autonomous system as a whole in the path, so there are not many such autonomous systems, and it is possible to send global information.
BGP routing method:
[A] Hot potato routing: selfishly thinking about sending the package out as soon as possible
AS0 receives a data packet, and according to the prefix, it will go to 10 where it will go. It must pass AS1 first, then AS2. However, there are many ways for AS0 to go to these gateways to get these prefixes. He will choose the one with the lowest cost to send it. For example, if he finds that it is closer to AS2, he will send it directly to AS2.
[B] Router selection algorithm
It's complicated, considering local preferences and using hot spots.
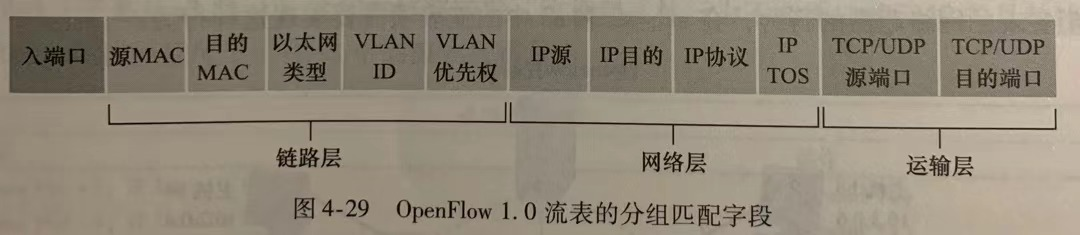
4. Packet switch: all-rounder, universal forwarding
A packet switch is different from a switch. A packet switch is more powerful. It is based on a flow table, which matches the set of header field values and counters to determine what action to take (which port to forward to, discard the copy or discard the packet, whether the modification is repeated Write some header fields). In this way, routing (selecting ports), layer 2 switching routing (changing the mac header), firewall (whether to discard packets), load balancing (which port to send to, rewriting certain fields), virtual network (similar to Rewrite the header field like NAT). It does not match some fields because it is useless and there is no need to increase complexity.
Intelligent Recommendation
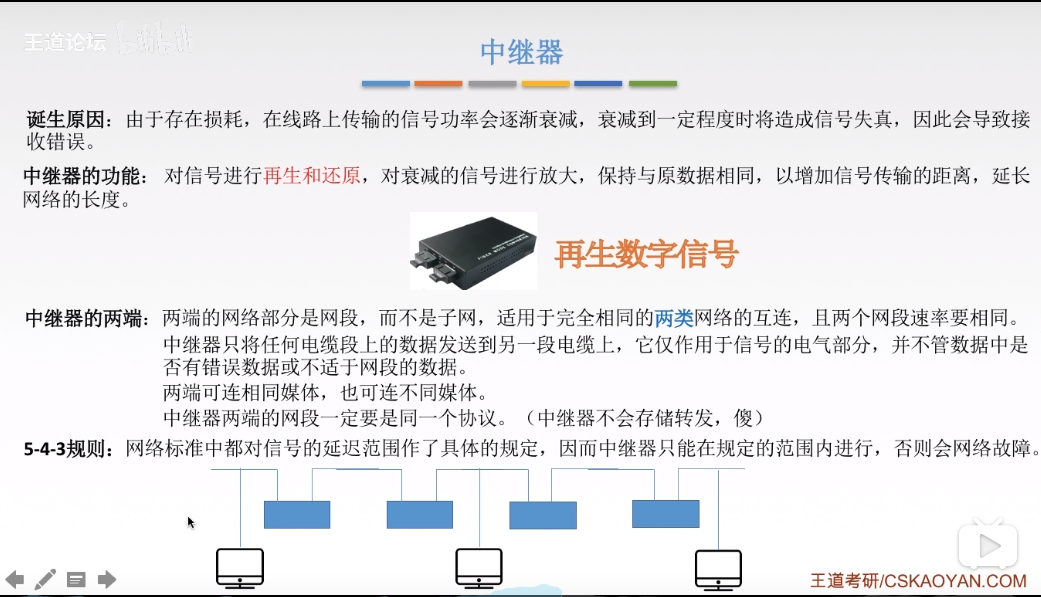
The physical layer repeater devices and hubs ---
[SeePubMed king videoNotes made] invasion deleted Repeater: The birth of reasons: because of loss of signal power transmission line of the road will gradually decay, will result in distortion of the s...
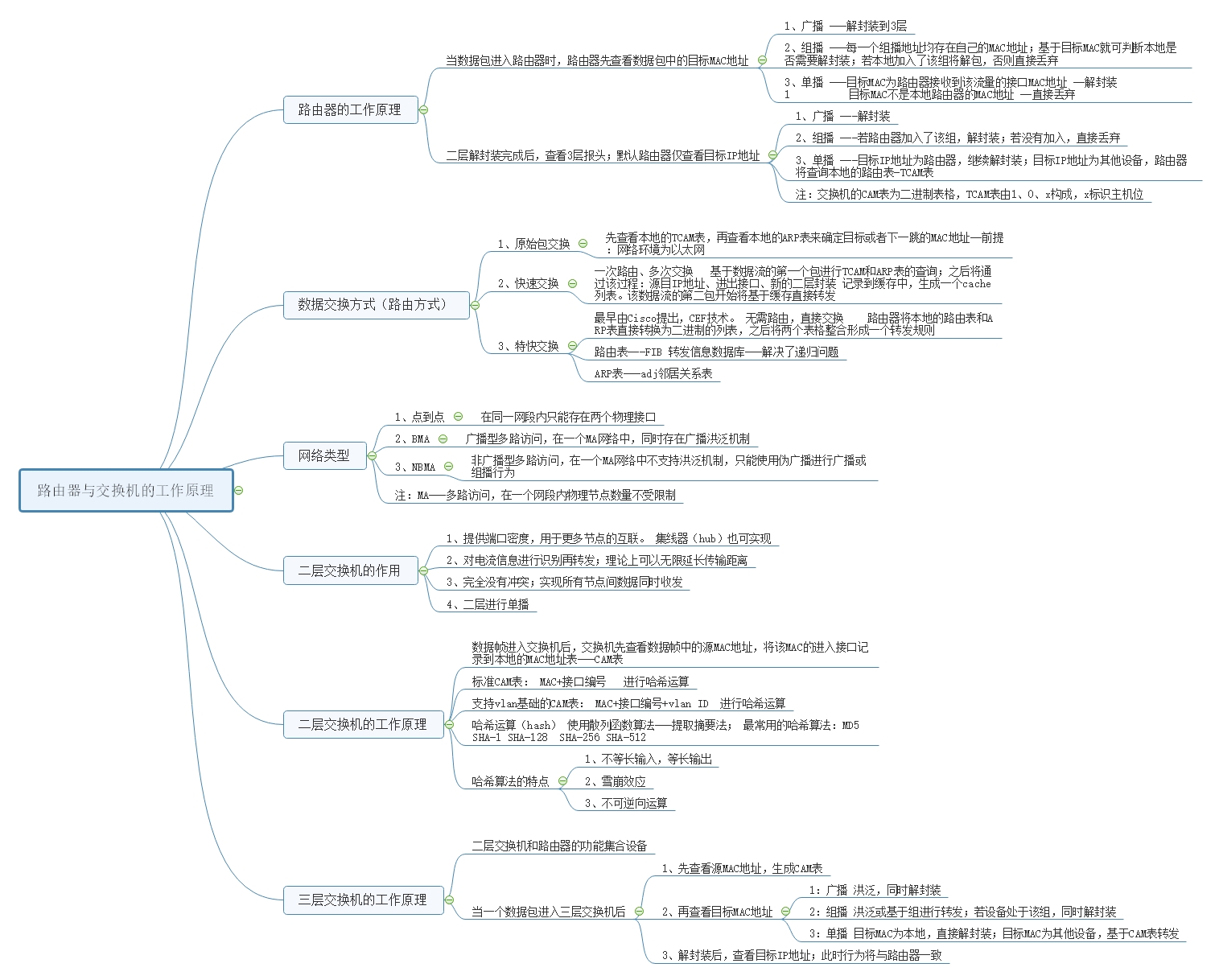
Working principle of routers, Layer 2 and Layer 3 switches
How the router works Router (Layer 3 equipment) When the packet enters the router, the router first checks the target MAC address in the packet; 1、broadcast -Decapsulation to 3 layers &nbs...
Computer network-physical layer equipment
Repeater: [No store and forward] [Regenerated digital signal] Hub: [multi-port repeater] [regeneration, amplifying signal] [The hub cannot divide the conflict domain】【Hosts connected to the sam...
"Computer Network - top-down" study notes - the network layer (IP, ICMP, DHCP, RIP, OSPF, etc.)
1, an overview of the network layer The main function of the network layer forwarding (data input interface from the router transferred to a suitable output interface) and routing (routing-end), each ...
ICMP protocol at the network layer (Layer 3)
table of Contents 0. Related articles: 1. Overview of the ICMP protocol 2. Introduction to the ICMP protocol 3. Functions of ICMP protocol 0. Related articles: ICMP(Baidu Encyclopedia) Detailed explan...
More Recommendation
Hubs, switches, and routers
1. The hub works in the physical layer of the computer network, the switch works at the data link layer, and the router works at the network layer. 2. A router is a special computer with a complete TC...
Hubs, switches and routers
1. Explanation of terms: Hub: (Hub) refers to the connection of multiple Ethernet twisted pairs or optical fibers in theUnder the same physical mediumdevice of. The hub happens atPhysical layer。 switc...
[Computer network] Network layer: BGP protocol (Introduction to BGP protocol | BGP protocol information exchange | BGP protocol message format | BGP-4 common messages | RIP, OSPF, BGP protocol comparison)
Article Directory 1. Classification of routing protocols 2. Introduction to BGP Protocol 3. BGP protocol information exchange process 3. BGP protocol message format 4. BGP protocol features Five, the ...
Principle and configuration of single-arm routing (interoperability between Layer 3 switches and routers throughout the network)
Experiment two single-arm routing principle and configuration (three-layer switch and router are interconnected throughout the network) lab environment Purpose Experimental steps Step 1: Configuration...
Network layer-IP, ICMP protocol summary
IP, ICMP protocol 1.IPv4 protocol 1.1IPv4 header IP datagram format (header structure) Header length: 4 bits, which can represent 2^4-1=15 units (one unit is 4 bytes), that is, the maximum length of t...