How do I determine how long should I use when you want to create a prefix index to a string?
tags: MySQL String index database
table of Contents
Add string index and prefix index
Add a string index:alter table SUser add index index1(email);
Contains the entire string of each record in index index1
Add a prefix index:alter table SUser add index index2(email(6));
For each record in Index2, only the first 6 bytes
Use prefix index shortcomings and advantages
Disadvantages: The prefix index may increase the scan line, because the less n bytes in the prefix index, the less scan lines are small
advantage: That is to say, use the prefix index, define the length, you can save space, no additional increase in more
inquiry cost.
How to determine how long the prefix is used
In fact, we pay attention to the establishment of an index.distinctionThe higher the distortion, the better. Because the higher the distortion, the less key value is repeated. Therefore, we can determine how many different values in the statistical index can be judged to use.
Check for phrases:SELECT Count (Distinct String Field) AS L from Name;
segmentation The value of the prefix:Select Count (Distinct Left (Field Name, Front K)) AS column name from the FROM table;
Query the value of different prefixes in the DEV table
mysq1> select
->count(distinct left(cpuid,2as L2,
->count(distinct left(cpuid,3 as L3,
->count(distinct ieft(cpuid,4 as L4,
->count(distinct left(cpuid,6as L6,
->count(distinct left(cpuid,10) as L10,
->count(distinct left(cpuid,12))as L12
->from dev ;
+——-—-+-—--——+-—-——-+-—-———+------+-—--——+
| L2 | L3 | L4 | L6 | L10 | L2 |
+——-—-+-—--——+-—-——-+-—-———+------+-—--——+
| 750 | 1175 | 1191 | 1192 | 1195 | 1195 |
+-———-+-——--—+-——---+-———--+-—--—-+——-—--+
1 row in set (0.03sec)
As you can see from the results of the query The value corresponding to the time is basically close, so if you want to add a CPUID string field as an index, you only need to intercept the first 4 characters.
Intelligent Recommendation
Why do you want malloc()? When do you want malloc()? How do you use malloc()?
Comments from all parties: malloc free is a C library function C++ is basically not used C ++ Use new , delete operator c++ originally did not advocate the use of malloc, but with new, after all, mall...
You know how Null in SQL, what should I do?
When you use the database to do business development, you often encounter keywords."null";Thatnulland""what differences are there?nullWhat is usually used? currently usingnullDurin...
There is no this in Vue3, what should I do if I want to use this?
Use the getCurrenTINSTANCE function to obtain instance objects Recommended Useproxy Because of the use ofctxIt is used to replace this only for the development stage. If the project is packed and plac...
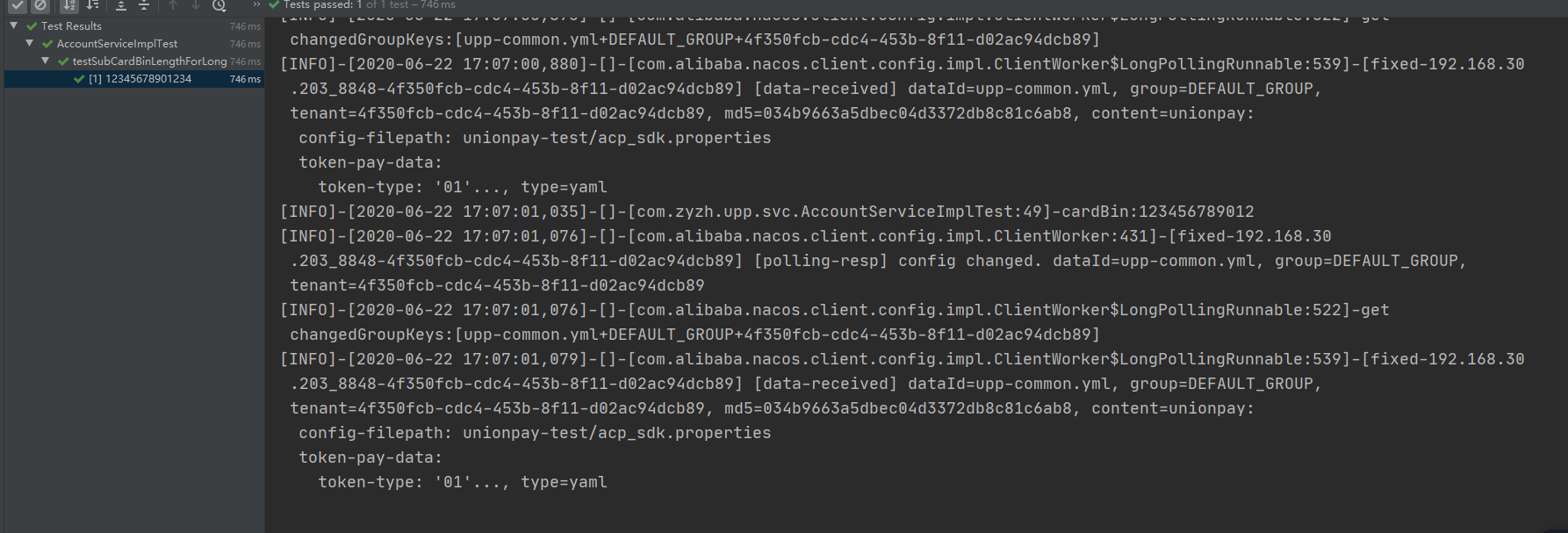
(Private method? I want to access it!) When the test needs to access the private method of the Service layer, you should do this!
(Private method? I want to access it!) When the test needs to access the private method of the Service layer, you should do this! Preface I was writing a test recently,TDD(Test Driven Development), an...
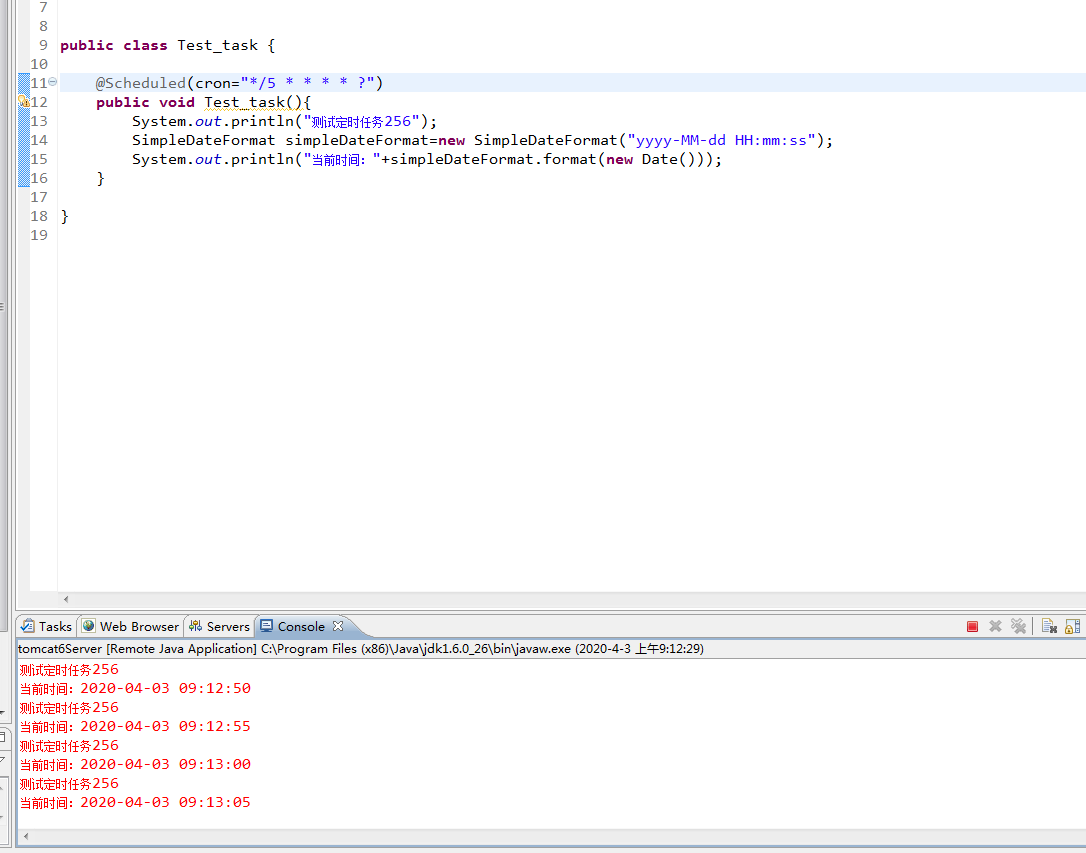
The next door renter (girlfriend) I let him do it, when, how long, and how I do it, I have perfect control
Cron expressions are mainly used in the Quartz framework. Quartz is an open source job scheduling framework written entirely by java. The main function is the scheduler (complete timing tasks), which ...
More Recommendation
Linux I just want to know how much you use
This article identifies:L00006 Edit this article: Tyrant Programming Tools : redhat6 Reading time:3 minutes · Positive· Text· Come · La · View disk space...
How to build an index prefix index in the Mysql long string
Because of the business needs, it is inevitable to match the relatively long fields. If the index is not established, full mete scan is performed, and it is very consumed. But establishing an index fo...
"Thinking in Java" - How do I create an object when private?
How do you create an object when the constructor is private? You can create through Static members, such as: or: You can create an object via a.construct () or b.construct (). wherein the second metho...
What should I do when I am confused? Use three thoughts to help you find the answer
Ask the question: Do you often think about the following questions? What are you going to do in the future? What is the point of learning? Upgrading from junior college or looking for a job? Postgradu...
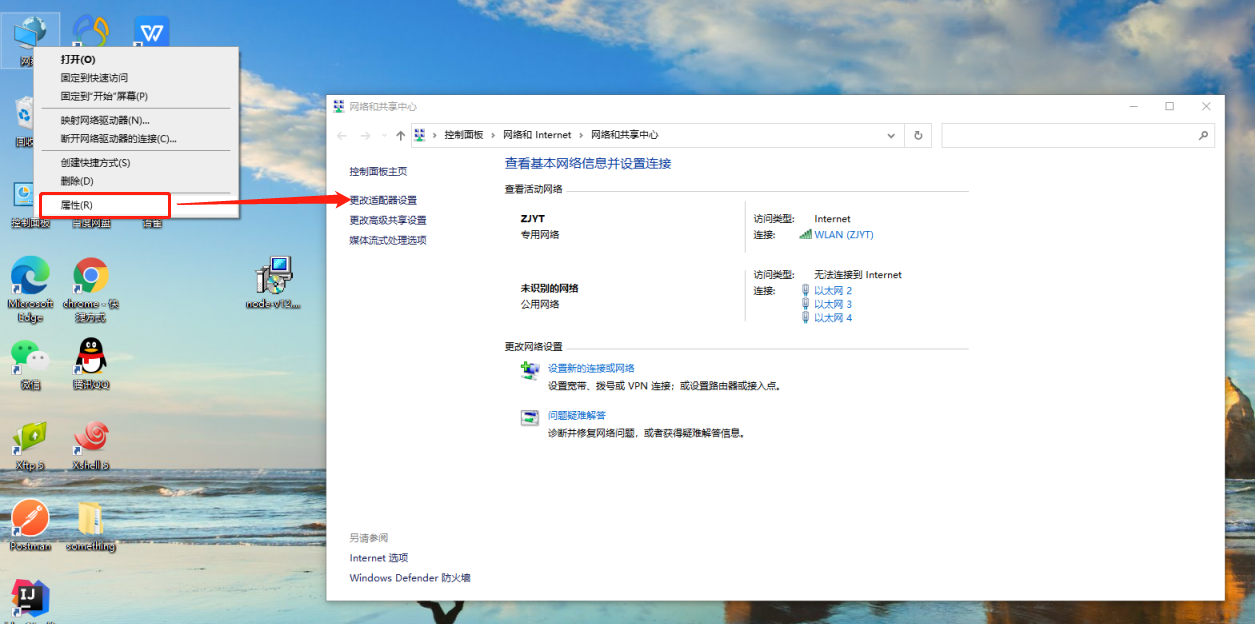
How do I connect to multiple VPNs at the same time? How many times do you want to connect?
In the enterprise, there are different projects, they are interdependent, maybe A project uses part of the B project, and uses part of the B project, this time, it is necessary to use VPN, however, ma...