Introduction and implementation of A5/1 encryption algorithm
1. Introduction to the algorithm
The A5/1 encryption algorithm is used for data confidentiality encryption in GSM. This algorithm uses three linear feedback shift registers, denoted as X, Y, and Z. Where X(x0, x1, …, x18) The register has 19 bits, the Y register has 22 bits, and the Z register has 23 bits. The following does not explain the principle, only the key stream generation algorithm.
- Define the X operation:
temp = x13 ^ x16 ^ x17 ^ x18
xi = xi-1 for i = 18, 17, 16, …, 1
x0 = temp; (In short, it is shifted one bit to the left, and then the first bit uses the x before shifting left13 ^ x16 ^ x17 ^ x18Filling, similar to the following)
Define Y operation:
temp = y20 ^ y21
yi = yi-1 for i = 21, 20, 19, …, 1
y0 = temp;
Define Z operation:
temp = z7 ^ z20 ^ z21 ^ z22
zi = zi-1 for i = 22, 21, 20, …, 1
z0 = temp; - Define the majority voting function maj(x, y, z): If the number of 0 in x, y, z is more, return 0; otherwise, return 1.
- Let m = maj(x8, y10, z10), if x8 = m, then perform X operation; if y10 = m, then perform Y operation; if z10 = m, then perform the Z operation.
- Keystream bits s = x18 ^ y21 ^ z22。
- Repeat the above steps to generate the key stream.
2. Simple implementation
A simple realization with C++, put a main.cpp text file encryption and decryption in the same directory of the code.
#include <cstdio>
#include <iostream>
#include <cstdlib>
#define _for(i,a,b) for(int i=(a); i<(b); ++i)
#define setbit(x,y) x|=(1<<y)
#define clrbit(x,y) x&=~(1<<y)
#define reversebit(x,y) x^=(1<<y)
#define getbit(x,y) (x&=(1<<y))
using namespace std;
typedef unsigned char uc;
bool x[19] = {1,0,1,0,1,0,1,0,1,0,1,0,1,0,1,0,1,0,1};
bool y[22] = {1,1,0,0,1,1,0,0,1,1,0,0,1,1,0,0,1,1,0,0,1,1};
bool z[23] = {1,1,1,0,0,0,0,1,1,1,1,0,0,0,0,1,1,1,1,0,0,0,0};
int maj(bool x, bool y, bool z) {
return x + y + z >= 2;
}
void X(bool x[]) {
bool temp = x[13] ^ x[16] ^ x[17] ^ x[18];
for(int i = 18; i >= 1; i--) {
x[i] = x[i-1];
}
x[0] = temp;
}
void Y(bool y[]) {
bool temp = y[20] ^ y[21];
for(int i = 21; i >= 1; i--) {
y[i] = y[i-1];
}
y[0] = temp;
}
void Z(bool z[]) {
bool temp = z[7] ^ z[20] ^ z[21] ^ z[22];
for(int i = 22; i >= 1; i--) {
z[i] = z[i-1];
}
z[0] = temp;
}
uc* generateSecretKeyStream(int n) {
bool temp[8];
uc* secretKeyStream = (uc*)malloc(n/8 + 1);
int cnt = 0, cnt1 = 0;
_for(i, 0, n) {
bool m = maj(x[8], y[10], z[10]);
if(x[8] == m) {
X(x);
}
if(y[10] == m) {
Y(y);
}
if(z[10] == m) {
Z(z);
}
bool s = x[18] ^ y[21] ^ z[22];
temp[cnt++] = s;
if(cnt == 8) {
_for(j, 0, cnt) {
if(temp[j] == 0) {
clrbit(secretKeyStream[cnt1], j);
} else {
setbit(secretKeyStream[cnt1], j);
}
}
cnt1++;
cnt = 0;
}
}
_for(j, 0, cnt) {
if(temp[j] == 0) {
clrbit(secretKeyStream[cnt1], j);
} else {
setbit(secretKeyStream[cnt1], j);
}
}
return secretKeyStream;
}
int getFileSize(FILE *fp) {
fseek(fp, 0L, SEEK_END);
int size = ftell(fp);
fseek(fp, 0L, 0);
return size;
}
uc* readFromFile(FILE *fp, int size) {
uc *buffer = (uc *)malloc(sizeof(uc) * size);
fread(buffer, size, 1, fp);
return buffer;
}
int main(int argc, char const **argv) {
FILE* fp = fopen("main.cpp", "r");
if(!fp) {
return -1;
}
int fileSize = getFileSize(fp);
uc *buffer = readFromFile(fp, fileSize);
uc* secretKeyStream = generateSecretKeyStream(fileSize * 8);
_for(i, 0, fileSize) {
buffer[i] ^= secretKeyStream[i];
}
FILE* fp1 = fopen("secret.a51", "w");
fwrite(buffer, fileSize, 1, fp1);
_for(i, 0, fileSize) {
buffer[i] ^= secretKeyStream[i];
}
FILE* fp2 = fopen("_secret.a51", "w");
fwrite(buffer, fileSize, 1, fp2);
fclose(fp);
fclose(fp1);
fclose(fp2);
free(buffer);
return 0;
}
Intelligent Recommendation
RSA-Brief introduction of encryption algorithm and JAVA implementation
[1] Introduction to RSA The RSA public key encryption algorithm was proposed by Ron Rivest, Adi Shamir and Leonard Adleman in 1977. It was first announced in the United States in July 1987, when all t...
SHA-Brief introduction of encryption algorithm and JAVA implementation
[1] Introduction to SHA Secure Hash Algorithm (SHA) is a secure hash algorithm certified by FIPS. An algorithm that can calculate a fixed-length character string (also called a message digest) corresp...
MD5-Brief introduction of encryption algorithm and JAVA implementation
[1] What is MD5 MD5 stands for Message-Digest Algorithm 5 (message-digest algorithm 5), which is used to ensure complete and consistent information transmission. It is one of the hash algorithms (also...
RSA encryption algorithm brief introduction and Python implementation
RSA encryption algorithm brief introduction Note: This article is only a personal summary of myself after I have finished the RSA password. If there is an incorrect place, welcome to the OVO RSA is a ...
Implementation of RSA encryption algorithm (1)
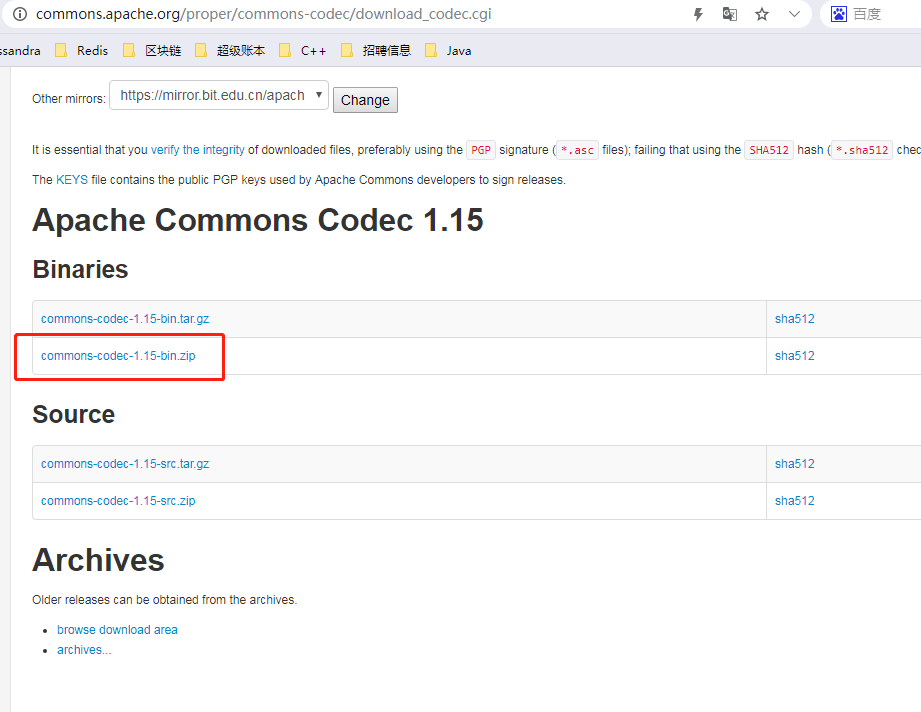
Write a custom catalog title here Import the required jar package 1. Download the jar package that Base64 depends on 2. Download the jar package that IOUtils depends on 3. Import dependent packages in...
More Recommendation
Elliptic Curve Encryption Algorithm Introduction 1--Symmetric Encryption and Asymmetric Encryption
Recently, I have been involved in elliptic curve encryption in my work. I started to understand the concept of encryption in detail. The purpose of this blog is to record the process of my study and t...
Encryption decision algorithm Java implementation (1) -base64
1, Maven Dependent 2, Java code...
Experiment 1 DES encryption algorithm programming implementation
South China University of Technology Software College Chen Chunhua (Dr.) [email protected] First, the experimental purpose Encrypt and decrypt the experimental data using the DES algorithm, mast...
Walking the rivers and lakes, safety first | Asymmetric encryption algorithm introduction and implementation
Walking on the rivers and lakes, safety first | Asymmetric encryption algorithm design and implementation I. Introduction and implementation of asymmetric encryption algorithms (1) Introduction to asy...