Introduction to common encryption algorithms
tags: Java development encrypt and decode Cryptography
Introduction
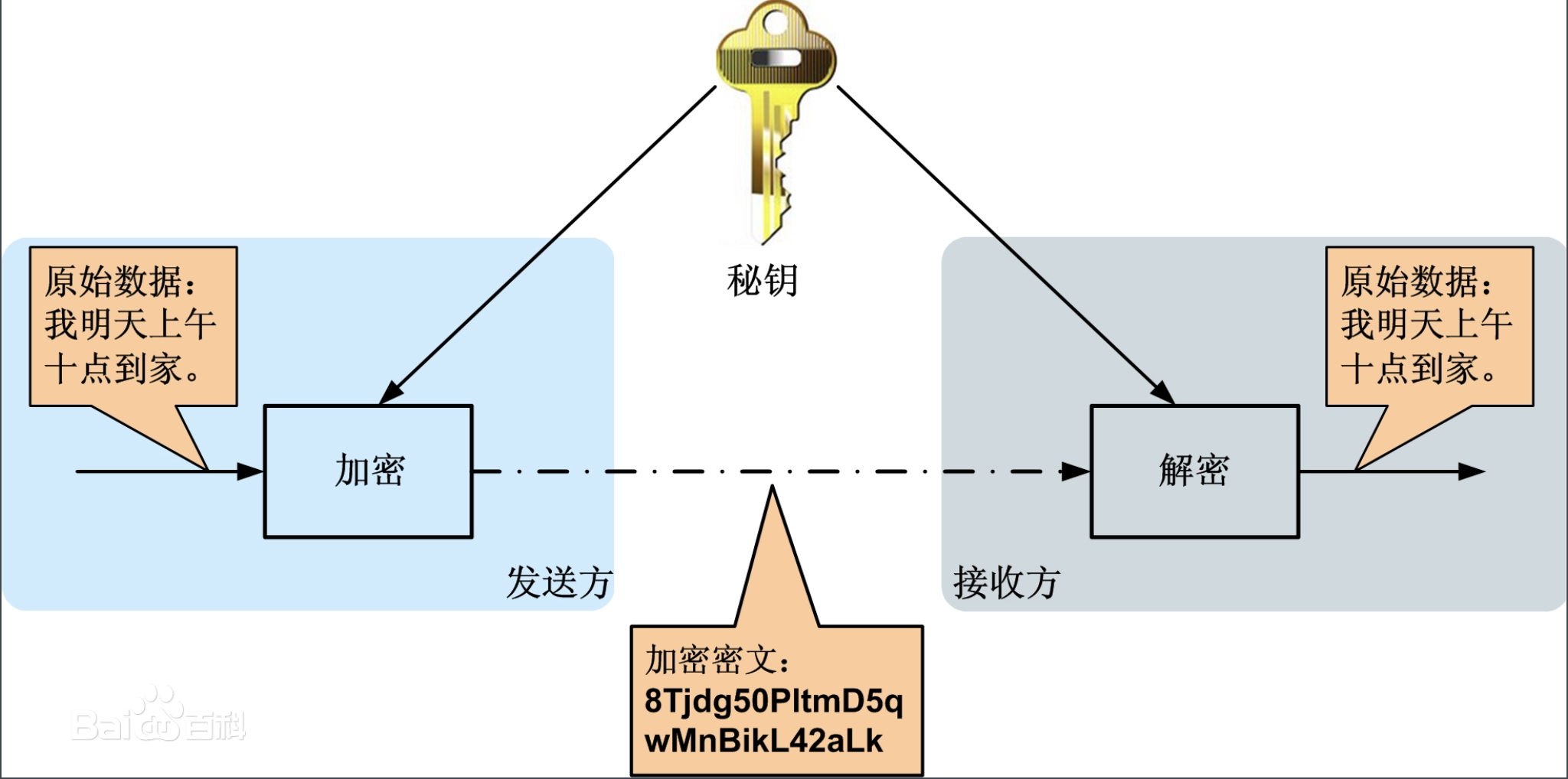
As a developer, it is necessary to understand some encryption algorithms. Through encryption algorithms, we can accomplish three goals of data communication, namely data confidentiality, data integrity, source and target user's legality, The common encryption algorithm types can be roughly divided into three categories:Symmetric encryption,Asymmetric encryption,One-way encryption
Symmetric encryption algorithm
The encryption key of the encryption algorithm and the decryption algorithm are the same, that is, the encryption and decryption keys are the same. In the communication process, the data sender divides the original data into fixed-size blocks, encrypts them one by one with the key and encryption algorithm, and sends them to the receiver; after receiving the encrypted message, the receiver combines the key and decryption algorithm The original data is obtained after decrypting the combination. Since the encryption and decryption algorithms are public, in this process, the secure transmission of the key becomes crucial. The key is usually negotiated by the two parties and passed to the other party in a physical manner. Then, once the key is leaked in this process, the data content will be exposed.
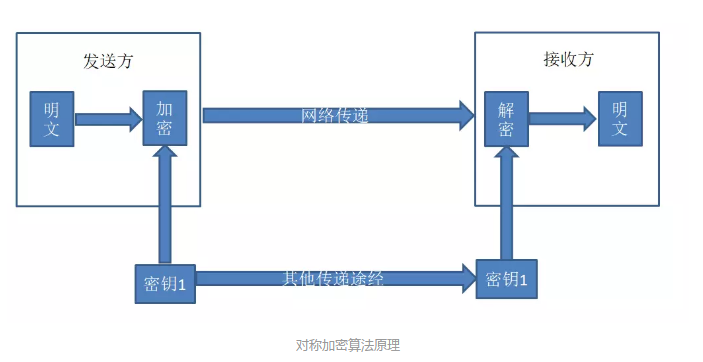
Symmetric encryption algorithm has the advantages of open algorithm, small calculation amount, high encryption speed and high efficiency, but also has the disadvantages of single key and difficult key management.
Common symmetric encryption algorithms:
DES: Packet encryption algorithm, which encrypts data in 64-bit packets, and uses the same algorithm for encryption and decryption.
3DES: Triple data encryption algorithm, three DES encryption algorithms are applied to each data block.
AES: Advanced encryption standard algorithm, is a block encryption standard adopted by the US federal government, used to replace the original DES, has been widely used.
Asymmetric encryption algorithm
The asymmetric encryption algorithm uses two different passwords for public and private keys for encryption and decryption. The public key and private key exist in pairs. The public key is extracted from the private key and made public to everyone. If the public key is used to encrypt data, only the corresponding private key can be decrypted, and vice versa. The security of this simple asymmetric encryption algorithm is higher than that of the symmetric encryption algorithm, but its shortcoming is that it cannot confirm the legitimacy of the source of the public key and the integrity of the data.
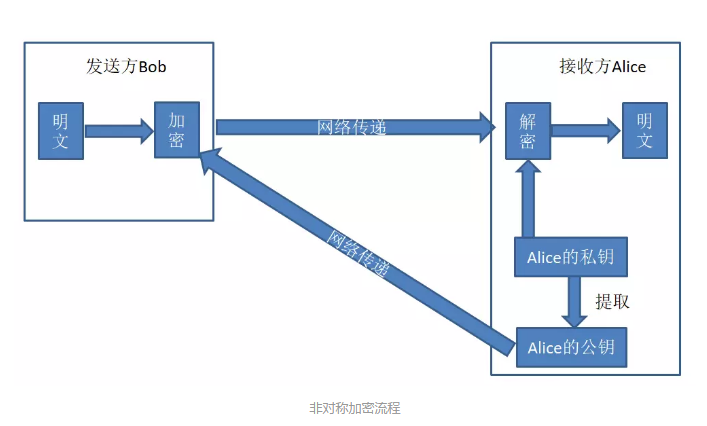
The asymmetric encryption algorithm has the advantages of high security and negative complexity of the algorithm strength. Its disadvantage is that encryption and decryption take a long time and slow speed, and it is only suitable for encrypting a small amount of data
Common asymmetric encryption algorithms:
RSA: The RSA algorithm is based on a very simple number theory fact: it is very easy to multiply two large prime numbers, but at that time it was extremely difficult to factorize the product, so the product can be publicly used as an encryption key and can be used for Encryption can also be used for signatures. This algorithm can resist all currently known password attacks.
DSA: Digital signature algorithm, which can only be used for signatures, not for encryption and decryption.
DSS: Digital signature standard. Skills are used for signatures, and can also be used for encryption and decryption.
ELGamal: Use the principle of discrete logarithm to encrypt or decrypt data or sign data, and the speed is the slowest.
One-way encryption algorithm
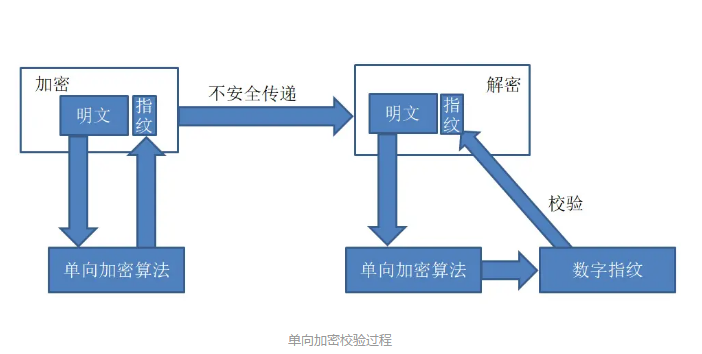
One-way encryption algorithms are often used to extract data fingerprints and verify the integrity of data. The sender encrypts the plaintext through a one-way encryption algorithm to generate a fixed-length ciphertext string, and then passes it to the receiver. After receiving the encrypted message, the receiver decrypts it and encrypts the plaintext obtained by decryption using the same one-way encryption algorithm to obtain an encrypted ciphertext string. Then compare it with the ciphertext string sent by the sender. If the ciphertext string before and after sending is consistent, it means that the data in the transmission process is not damaged; if it is inconsistent, it means that the data is lost in the transmission process. The one-way encryption algorithm can only be used to encrypt data and cannot be decrypted. It is characterized by fixed-length output and avalanche effect. The reason why one-way encryption is often used is that only brute force cracking is possible to unlock the encryption.
Note: The inability to crack the encryption algorithm means that it does not have the conditions for realization in space and time. If an encryption algorithm uses a critical attack and it takes 50 years under the existing computing resources, then it can be considered that it cannot be cracked. Or, the cost of cracking is far more than the resources protected by the password. There is value, then we can also say that it cannot be cracked.
Common one-way encryption algorithms:
MD5: MD5 is actually a hash algorithm, which essentially generates a message digest of a piece of information to prevent the information from being tampered with. Strictly speaking, MD5 is not an encryption algorithm but a digest algorithm. No matter how long the string is, MD5 will output a string with a length of 128 bytes, which is 32 characters when converted to hexadecimal.
SHA-1: The SHA-1 algorithm is the same message digest algorithm as MD5, but SHA-1 is more secure than MD5. SHA-1 will generate a 160-bit message digest with 40 characters in hexadecimal, so SHA1 is currently the most secure digest algorithm.
Intelligent Recommendation
Common encryption algorithms and examples
Encryption and decryption are often used in development, and it is good to be familiar with it. Article Directory One-way hashing algorithm md5 DigestUtils (spring) implement md5 Symmetric encryption ...
Common symmetric encryption algorithms
The essence of data encryption is to confuse and conceal the original information content to make it difficult to understand or reverse decryption, or it cannot be decrypted in a short period of time ...
Java common encryption algorithms
Common encryption algorithms BASE64, MD5, SHA, and HMAC are several encryption algorithms. The BASE64 encoding algorithm is not a real encryption algorithm. MD5, SHA, HMAC these three encryption algor...
Summary of common encryption algorithms
Message summary Message Digest is also known as Digital Digest It is a fixed-length value that uniquely corresponds to a message or text, which is generated by a one-way Hash encryption function actin...
Common encryption rules and algorithms
Commonly non-reversible juvenile algorithm (is an encryption algorithm, not encrypted rules): Commonly symmetrical encryption (encrypted decryption is the same key): Commonly used asymmetrical encrypt...
More Recommendation
Common encryption algorithms and common encryption algorithm principles
Encryption algorithms and protocols Symmetric encryption Introduction: Encryption and decryption use the same key Common algorithms: - DES:Data Encryption Standard; - 3DES:Triple DES; - AES:Advanced E...
Summary of Common Algorithms of "Introduction to Algorithms"
Foreword: Many other blog contents are used in the summary of this article. I originally wanted to attach the original link, but I haven't found it for a long time. The originality here comes from the...
Introduction to symmetric and asymmetric encryption algorithms
1. Symmetric encryption algorithm: There is only one key used, and both sender and receiver use this key to encrypt and decrypt data, which requires the decryption party to know the encryption key in ...
Basic introduction to symmetric encryption algorithms
Symmetric encryption algorithm Using the encryption method of single-key cryptography, the same key can be used for encryption and decryption at the same time. This encryption method is called symmetr...
Common encryption and decryption algorithms - MD5
Java MD5 encryption Common encryption and decryption algorithms - MD5 First, MD5 encryption overview Message Digest Algorithm MD5 (Chinese name message digest algorithm fifth edition) is a hash functi...