Introduction of common hashing algorithms
tags: Distributed algorithm Consistent hash Node balance redis slot
background knowledge:
- Hash algorithms are mainly used in cache distributed systems.
- Distributed means that a whole is divided into multiple parts, which are executed by multiple servers. Pay attention to the difference with the cluster. The cluster is to deploy multiple identical wholes on multiple servers to execute independently.
- This article mainly uses key-value cache as an example to explain
1. Node balance: If you have 3 cache servers, numbered 0, 1, 2, the way of node balance is to hash the key and take the return value with 3 (the number of servers), according to Value assigns value to the corresponding numbered server. E.g:
For example, I have 6 keys, namely: 1, 2, 3, 4, 5, 6. According to the above description (assuming that the return value of the hash function is the value of key), we can easily calculate the distribution of the following values:
Server 0 Server 1 Server 2
key 3,6 1,4 2,5
Note: key=3 will be assigned to server 0 after the remainder operationHowever, it should be noted that the fault tolerance and scalability of node redundancy are not good. How to understand it, we still give examples:
Fault tolerance: For example, one day my No. 2 server went down and could not provide services, so I need to remove it and re-arrange the remaining servers.
Immediately after that, the remainder algorithm also changes accordingly, that is, the result obtained with the remainder of 2 is:
Server number 0 server number 1
key 2,4,6 1,3,5
Scalability: For example, because our cache server can no longer meet the business requirements, an additional server is added, and the surplus algorithm also occurs correspondingly
After the change, that is, taking the remainder with 4, the result is:
Server 0 Server 1 Server 2 Server 3
kay 4 1,5 2,6 3
We all know the cache service. When the value corresponding to the key does not exist, it will obtain data from the source (for example, from mysql), and then store it in the cache and return
To the client, if the value corresponding to the key exists, it is directly returned to the client. Based on this principle, it is assumed that when three servers, we have already 1-6
The value corresponding to each key is set in the corresponding server. At this time, due to the downtime, the server has become two. According to the distribution relationship analyzed above, we
If you want to get the value corresponding to 2, it will be assigned to the No. 0 server to obtain, but the No. 0 server is not stored (because the value corresponding to 2 is in three services
It is stored in the server with the number 2), so the result is that the cache does not hit, that is, to obtain data from the source.
From the above analysis, it is not difficult to find that if the server node changes in this way, the cache hit rate will decrease, so don’t mind using it
If you want to use it, it is recommended to expand the node twice as much as the original node.2. In order to solve the problem that a large number of caches cannot be hit when the number of servers remaining in the node is changed, a consistent hash appears, and the consistent hash is to design the entire hash value into a closed ring. And the server node is mapped on the ring with a hash function. When a key comes over, it is also mapped on the ring using the same algorithm. Some people may ask, which server does this key belong to? Clockwise according to the current mapped position of the key, the first server encountered is the server where the value corresponding to the key is stored. For details, you can check the following figure (ignore the watermark in the lower left corner of the picture, the pink circle is the key mapping position on the ring, and the white and cyan circle is the node mapping position on the replacement)
Although consistent hashing solves the problem that a large number of caches cannot be hit due to changes in the number of residual servers, and relatively good fault tolerance and scalability, it still causes the problem that a small portion of cached data cannot be hit. It needs attention. (This is why redis does not use a consistent hash algorithm but uses a virtual slot as an alternative solution, because the virtual slot technology makes the slot point managed by each node fixed, even if you add a node, you need other nodes to change the slot. Points are assigned to the new node, and the new node is eligible to manage the slot, so there will be no data loss problem).
Intelligent Recommendation
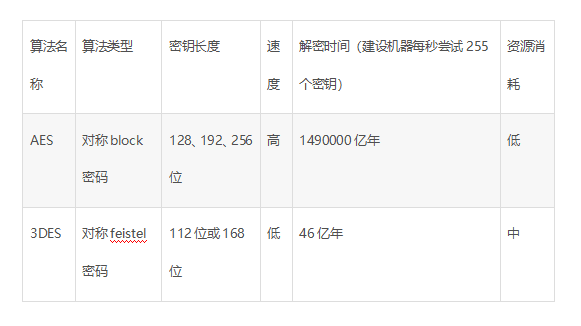
Introduction to common algorithms for data encryption
data encryption Foreword 1.MD5 encryption 2.RSA encryption 3. AES encryption 4. 3DES encryption Foreword Whether user data is stored in SharePreferences or in a SQLite database, it is necessary to enc...
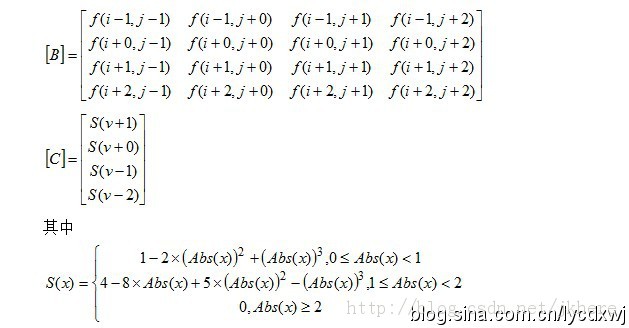
Introduction to common interpolation algorithms (3)
2019 Unicorn Enterprise Heavy Gold Recruitment Python Engineer Standard >>> Bicubic interpolation (also called coordination plate element), the binary bicubic interpolation formula has a tota...
Introduction to several common GC algorithms
This article is mainly about the commonly used GC algorithm (Reference counting、Mark-sweep、Replication algorithm、Mark-sweep algorithm) Make relevant explanations and give a brief introduction to relev...
Introduction to Scala _ common algorithms for arrays
Array common algorithm The array in scala encapsulates some commonly used calculation operations, and we do not need to reimplement it ourselves when processing data in the future. The following are s...
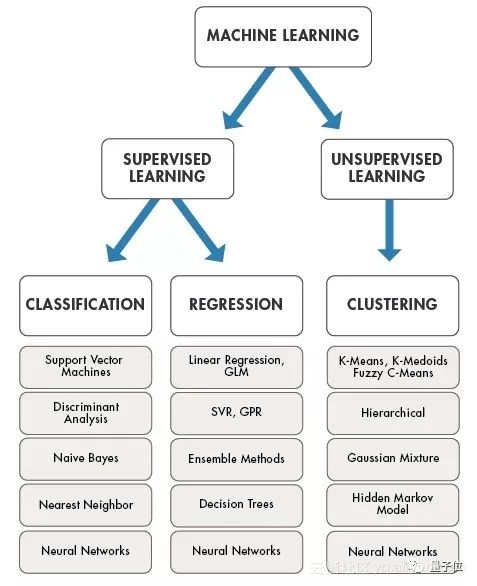
An introduction to common machine learning algorithms
This article comes from AI new media qubit (QbitAI) The so-called machine learning algorithm is a set of hypotheses used to find the optimal model. Machine learning algorithms can be divided into thre...
More Recommendation
Introduction to the principles of common sorting algorithms
Common sorting algorithm principle study notes Bubble Sort Quick sort Insertion sort Hill sort Select sort Merge sort Base sort Heap sort Implementation of each sorting algorithm code Bubble Sort Comp...
Introduction to eight common sorting algorithms
Direct insertion sort Algorithm idea First, compare the second number with the first number. If the second number is smaller than the first number, insert the second number before the first number to ...
Introduction and implementation of common search algorithms
Common search algorithms: Sequential (linear) search Binary search/binary search Interpolation lookup Thinking analysis: Traverse the array from beginning to end, and return the array index when found...
Introduction to Map collection and common algorithms
Article Directory HashMap TreeMap Common algorithms Several ways to convert json to map Features of Map collection: * 1. Unordered * 2. Data storage by key-value pair * 3. The key is unique and the va...
Classification and introduction of common encryption algorithms
1. Classification of encryption algorithms Does not consider decryption issues at all; Private key encryption technology: Symmetric Key Encryption: Symmetric encryption uses the same key for encryptio...