libpcap packet capture analysis project (2)
In project (1), we successfully captured the data packet and extracted the basic information in the data packet. This time we will output the various protocols used by the data packet and output the meaning of each layer of protocol. (In fact, just write a Wireshark).
In order to output the meaning of the information of each layer, let's first understand the PDU header of each layer:
- Ethernet frame header

- IP datagram header:

- TCP datagram:

- UDP datagram:

In my code, I quoted some Linux system library header files without rewriting the header files myself. The library files can go to the / usr / include / linux directory to find ip.h, tcp.h and udp. Useful header files such as h help everyone understand.
More detailed comments are given in the code. I hope to be helpful.
#include <stdio.h>
#include <stdlib.h>
#include <pcap.h>
#include <time.h>
#include <unistd.h>
#include <errno.h>
#include <sys/socket.h>
#include <netinet/in.h>
#include <arpa/inet.h>
#include <netinet/if_ether.h>
#include <linux/ip.h>
#include <linux/tcp.h>
#include <linux/udp.h>
// Output Ethernet frame header information
void print_ether_header_info(struct ether_header *eptr){
int i;
u_char *ptr;
printf("Enthernet II:\n");
ptr = eptr->ether_dhost;// Destination MAC address
i = ETHER_ADDR_LEN;
printf("Destination MAC addres: ");
do{
printf ("%s%02x", (i == ETHER_ADDR_LEN)?"":":", *ptr++);
}while(--i>0);
printf ("\n");
ptr = eptr->ether_shost;// Source MAC address
i = ETHER_ADDR_LEN;
printf("Sourse MAC address: ");
do{
printf ("%s%02x", (i == ETHER_ADDR_LEN)?"":":", *ptr++);
}while(--i>0);
printf("\n");
printf("Enthernet type: %#04x ",ntohs(eptr->ether_type));// Load type
if(ntohs(eptr->ether_type) == ETHERTYPE_IP)
printf("(IPv4)\n");
else if(ntohs(eptr->ether_type) == ETHERTYPE_ARP)
printf("(ARP)\n");
else if(ntohs(eptr->ether_type) == ETHERTYPE_REVARP)
printf("(RARP)\n");
else
printf("(Other)\n");
}
// Output IP header information
void print_ip_header_info(struct iphdr *ipptr){
struct in_addr addr;
char *c;
c = (char *)(ipptr);
printf("\nInternet Portocol:\n");
printf("Version: %d\n",ipptr->version);//version number
printf("Header length: %d\n",ipptr->ihl);// Head length
printf("Total length: %d\n",ntohs(ipptr->tot_len));// Total length
printf("Identification: %#04x\n",ipptr->id);// Authentication
c += 6;
printf("Flags: 0x%02x%02x",(*c),(*(c + 1)));// Flag DF, MF
if((*c)==0x40&&(*(c+1))==0x00)
printf(" Don't fragment\n");
else printf(" More fragment\n");
printf("Time to live: %d\n",ipptr->ttl);//TTL
printf("Protocol: ");// Transport layer protocol
if(ipptr->protocol == 1)
printf("ICMP(1)\n");
else if(ipptr->protocol == 2)
printf("IGMP(2)\n");
else if(ipptr->protocol == 6)
printf("TCP(6)\n");
else if(ipptr->protocol == 17)
printf("UDP(17)\n");
else printf("Unknow(%d)\n",ipptr->protocol);
printf("Header checksum: %#04x\n",ipptr->check);// Checksum
addr.s_addr = ipptr->saddr;
printf("Source IP address: %s\n",inet_ntoa(addr));// Source IP address
addr.s_addr = ipptr->daddr;
printf("Destination IP address: %s\n",inet_ntoa(addr));// Destination IP address
}
// Output TCP header information
void print_tcp_header_info(struct tcphdr *tcpptr){
printf("\nTransmission Control Protocol(TCP):\n");
printf("Source port: %d\n",ntohs(tcpptr->source));// Source port
printf("Destination port: %d\n",ntohs(tcpptr->dest));// Destination port
printf("Seq: %u\n",ntohs(tcpptr->seq));//Confirmation Number
printf("Checksum: %#04x\n",tcpptr->check);// Checksum
}
// Output UDP header information
void print_udp_header_info(struct udphdr *udpptr){
printf("\nUser Datagram Protocol(UDP):\n");
printf("Source port: %d\n",ntohs(udpptr->source));// Source port
printf("Destination port: %d\n",ntohs(udpptr->dest));// Destination port
printf("Length: %d\n",ntohs(udpptr->len));//length
printf("Checksum: %#04x\n",udpptr->check);// Checksum
}
// Output data information
void print_data_info(int j,const struct pcap_pkthdr *pkthdr,const u_char *packet){
int i;
printf("\nData:\n");
for(i=0;j<pkthdr->len;i++,j++){
printf(" %02x",packet[j]);
if((i+1)%16==0)
printf("\n");
}
printf("\n");
}
//Callback
void print_info(u_char *user,const struct pcap_pkthdr *pkthdr,const u_char *packet){
int j,*id;
struct ether_header *eptr;
struct iphdr *ipptr;
struct tcphdr *tcpptr;
struct udphdr *udpptr;
j = 0,id = (int *)user;
printf("id: %d\n",++(*id));
printf("Packet length: %d\n",pkthdr->len);// The length of the packet
printf("Number of bytes: %d\n",pkthdr->caplen);// Number of packets
printf("Reciverd time: %s\n",ctime((const time_t *)&pkthdr->ts.tv_sec));// Time when the package was received
// Get the Ethernet frame header
eptr = (struct ether_header*)packet;
print_ether_header_info(eptr);
j += 14;
if(ntohs(eptr->ether_type) == ETHERTYPE_IP){
// Get IP packet header
ipptr = (struct iphdr *)(packet + sizeof(struct ether_header));
print_ip_header_info(ipptr);
j += ipptr->ihl;
if(ipptr->protocol == 6){
// Get tcp packet
tcpptr = (struct tcphdr *)(packet + sizeof(struct ether_header) + sizeof(struct iphdr));
print_tcp_header_info(tcpptr);
j += 20;
}else if(ipptr->protocol == 17){
// Get udp packet
udpptr = (struct udphdr *)(packet + sizeof(struct ether_header) + sizeof(struct iphdr));
print_udp_header_info(udpptr);
j += 20;
}else
printf("\nThis packet didn't use TCP/UDP protocol.\n");
}else
printf("\nThis packet didn't use IP protocol.\n");
// Get data, if it is not IP, not UDP / TCP, then treat the header of other protocols as data
print_data_info(j,pkthdr,packet);
printf("\n\n");
}
int main(){
char *device;
char errBuf[PCAP_ERRBUF_SIZE];
pcap_t *head;
int id;
device = "ens33";// Convert to ens33 network card
// Open the device device, the maximum number of bytes is 65535, it is not in promiscuous mode, and it does not return if it does not capture the data packet, and the error message
head = pcap_open_live(device,65535,0,0,errBuf);
if(head){
printf("Open device success!\n");
}else{
printf("Open device failed. %s\n",errBuf);
return 0;
}
// Wait for a packet to return
struct pcap_pkthdr packet;
const u_char *packetflag = pcap_next(head,&packet);
if(packetflag){
printf("Get a pcaket success.\n");
id = 0;
pcap_loop(head,1,print_info,(u_char *)&id);
}else{
printf("Get a pcaket failed. %s\n",errBuf);
pcap_close(head);
return 0;
}
// Turn off the device and return the resources
pcap_close(head);
return 0;
}


In this way, we parse the PDU header of each layer and output the meaning of the corresponding information in each header.
There is only one packet to try here, you can also set parameters to capture many packets to parse.
Intelligent Recommendation
IP packet capture library use Libpcap LAN
Experimental requirements Source and destination physical address of the print data packet; Print source IP and destination IP address; Printing upper layer protocol type; If the upper layer protocol ...
libpcap network packet capture function library
download Compile and install Instance The C function interface provided by the library is used to capture data packets passing through the specified network interface. download: http://www.linuxfromsc...
Design and implementation of network packet capture and traffic online analysis system-based on libpcap on MacOS Record this happy (DT) week
Design and implementation of network packet capture and traffic online analysis system-based on libpcap on MacOS Record this happy (DT) week Claim: Design and implement a network flow analysis system ...
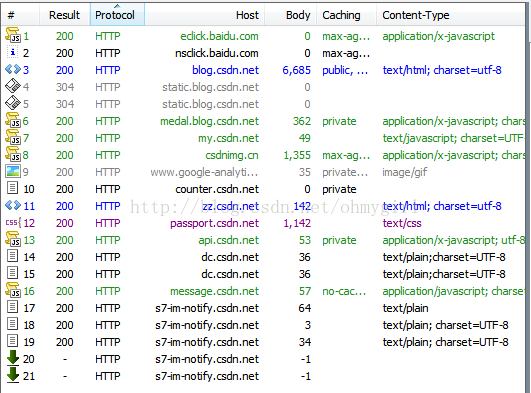
Fiddler (2) - Using Fiddler for packet capture analysis
Share my idol god's artificial intelligence tutorial! Also welcome to reprint my article, please indicate the source Fiddler (2) - Using Fiddler for packet capture analysis FirstBlog postThe principle...
Use Fiddler to do packet capture analysis (2)
Editor:Click on the link to open Fiddler HTTP request to fetch. Fiddler capture is the most basic applications to this blog, for example, after starting Fiddler, enter in your browser After hit enter,...
More Recommendation
TLS1.3 packet capture analysis (2)-ServerHello
Continuing with the last packet analysis, this time the main content is the ServerHello message in the TLS handshake. The first is the content of the Record Layer,Content TypeIndicates that the conten...
Network packet capture function library Libpcap installation and use (very powerful)
1. Introduction to Libpcap Libpcap is the abbreviation of Packet Capture Libray, which is the data packet capture function library. The C function interface provided by the library is used to capture...
WinPcap / libpcap network packet capture TCP header flag
Recent WinPcap / libpcap fetch packet network, and to extract HTML image. To analyze TCP packets when they were big-endian out of the head. Finally, patience and the flag bit fields are read out. TCP ...
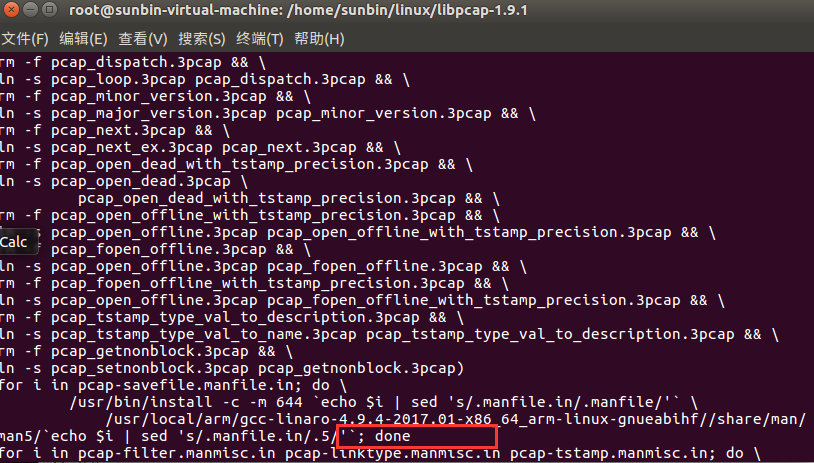
Porting libpcap packet capture library to arm platform under Linux
1. Introduction The libpcap library is installed on the x86-based Ubuntu. The predecessors have written very clearly. For details, please refer to: as well as If you need any dependency packages durin...
Libpcap library programming guide-network card packet capture
The functions and effects achieved by the sample program in this lecture are very similar to those in the previous lecture (open the adapter and capture data packets), but this lecture will use the pc...