Security lattice model based on information flow
tags: Computational Mathematics and Mathematical Theory Lattice model Information Flow
Security lattice model of information flow
1. Establish a lattice model of information flow
what isInformation Flow ?
Information FlowIs a set of information in the same direction in space and time, it hascommonofInformation SourcewithInformation recipient。
This model is common in military systems and government systems because they areFlow of informationHavestrictoflimit。
- bossOnlyAccept reports from subordinates,Can'tInform subordinates;
- Between different departmentsCan'tCommunicate with each other.
- Government departments as shown in the figure below. rightLine segment with arrowExpressinformationofflow。

| E.g:Different power rangesCan useSubsetExpress Wang: {One three subjects} Money: {One Section One Section, One Section Two Section, One Section Three Section} Li: {Two places } Feng: {Two places } Zhao: {One Section One Section, One Section Two Section, One Section Three Section, Two Sections } |
withOnedepartmentofDifferent membersmight haveDifferent permissions Different departmentsofDifferent membersmight haveSame level |
- set upInformation lattice model:
model:Different power rangesuseSubset latticeL1,Different levelsuseLinear gridL2. CorrectDescription of permissionsuseLinear gridwithSubset latticeofProduct L2 x L1
(a, b)≤(c,d) a≤c and b
D, that isThe same department and low level。
When only (a, b) ≤ (c, d), the information can be from (a, b)main bodyFlow permissions are (c, d)main body。
Simplify the above information flow model, as follows: (Use a representative meta representation at the same level in the same department)
 |
 |
The information grid model established is as follows:
(The only information flow scenario is the limitation set in the model, that is, only (a, b) ≤ (c, d), the information can be from the authority (a, b)main bodyFlow permissions are (c, d)main body)

Second, transform the original information flow into a lattice model
andreal worldMany streams of informationDoes not constitute a lattice model, But we can still passRemodelMake the original information flowInformation flow model. And the information flow after transformation is consistent with the original flow, and after transformation, we canBetter controlInformation systemFlow of information. For example:
 |
 |
From the comparison of the above figure, we can see that we first merged the BCH, and then added many nodes to make the entire information flow form a grid. For example, new nodes such as E∧F, E∨F, D∨G, and A∨I are added.
Intelligent Recommendation
Several difficult questions based on lattice
grid Definition of case Lattice is an algebraic structure based on partially ordered sets. It originated from Kepler's conjecture about the maximum density of equal-radius balls stacked in a container...
Hongyi Li——Flow-based Generative Model
Hongyi Li——Flow-based Generative Model Introduction Generative model already introduced Math background jacobian Matrix Determinant change of Variable Theorem flow-based generative model I...
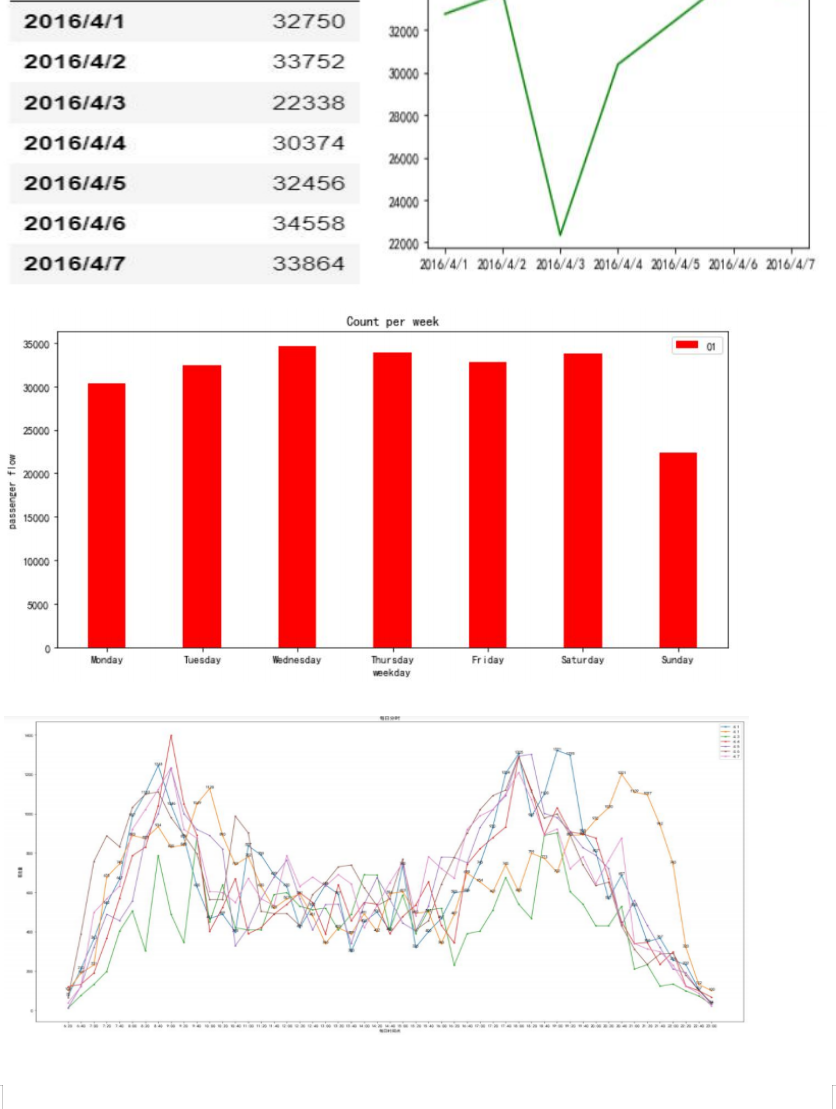
Passenger flow forecast based on ARMA model
This article mainly shares my own learning results. The content is not perfect and needs to be improved. Please consult vx:15660876350 for specific codes. The results can be used as a reference for pl...
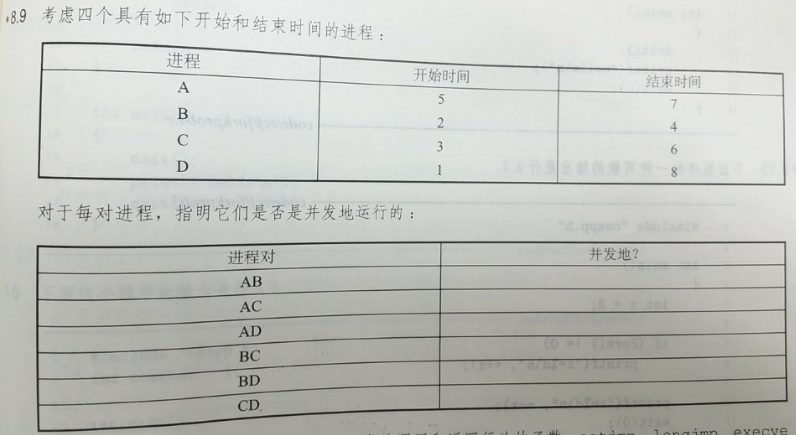
Information security system design based homework
"In-depth understanding of computer systems" homework * 8.9 answer: Process pair Whether it is concurrent AB no AC Yes AD Yes BC Yes BD Yes CD Yes * 8.10 answer: A. Call o...
Spring Security-database-based user information authentication
Spring Security-database-based user information authentication I. Introduction As mentioned in the previous article, you can configure user information through the application.properties configuration...
More Recommendation
Lattice modifier to create 3D DNA model (twisted twist, lattice)
Modifier used Distortion modifier Lattice modifier Production process Shortcut key: move the mouse to the view window and pressalt+wKey to maximize the view window Place the plane in the front view Se...
springboot - security authentication based on a custom database model
A, Maven configuration This example is based security5 + mybatis-plus + lombok Two, application.properties configuration Third, create a database table statement Four, security codes Fifth, test inter...
Paper - generation model GANs, VAEs, Flow-based Invertible Model
During the National Day happened to see an article on Unsupervised Blingual Lexicon Induction, except with the prior read the article, basic article before use GANs are generated as a model, generated...
lattice
Output in the grid The stringInGrid method prints the specified string in a grid of the specified size. requires the string to be centered in both horizontal and vertical directions. If the string is ...