Error type
Segmentation fault (core dumped)cause
Segmentation fault segment error.
Core Dump core dump (the operating system receive certain signals while the process terminates, the other elements of information at this time about the process address space and process state written to a disk file. This information is often used for debugging ) that the "nuclear spit" is the word to describe it properly, is the core of memory spit it out.
Possible reasons for this error (actually accesses the memory of things should not have access):
1, the memory access violation:
(1) out of bounds array access, since the mark is out of range.
(2) when the search string, the string by the end of the symbol to determine the end, but in fact no such terminator.
(3) strcpy, strcat, sprintf, strcmp, strcasecmp string manipulation functions, etc., exceeds the maximum range of characters that can be stored are defined. Use strncpy, strlcpy, strncat, strlcat, snprintf, strncmp, strncasecmp the like to read and write functions to prevent cross-border.
2, multi-threaded program using a thread-safe function.
3, multi-threaded data reads and writes unlocked protection.
For global data will be accessed by multiple threads at the same time, it should be noted that locking protection, or is likely to cause a core dump
4, invalid pointer
(1) using the NULL pointer
(2) Feel free to use pointer casts, because this cast is actually very safe, because you do not confirm this type should be transformed when you type, so it is easy to make mistakes, because you will be in accordance casts of access, which makes it possible to access the memory should not have access.
5, stack overflow
Do not use large local variables (because local variables are allocated on the stack), so likely to cause a stack overflow, stack and heap structural damage system, leading to inexplicable errors occur.
Resolved scene
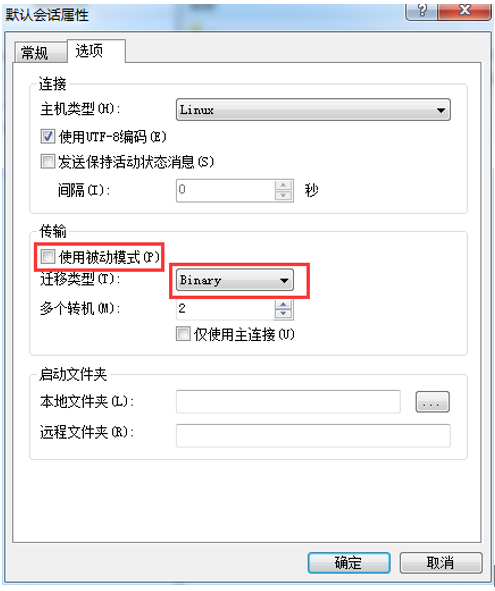
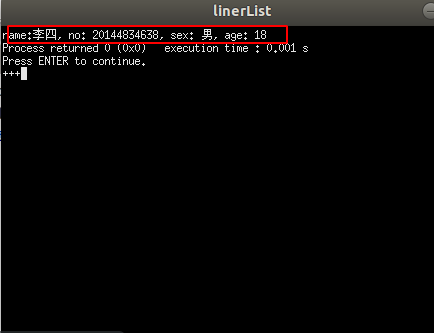
Linux on a virtual machine running a data structure, the above error occurs on a virtual machine, the Windows host pop-up error. So the same error occurs commissioning simple hash function like a virtual machine ,, noticed the following code:
// generates a hash value for a sting
// same as djb2 hash function
unsigned int CountMinSketch::hashstr(const char *str) {
unsigned long hash = 5381;
int c;
while (c = *str++) {
hash = ((hash << 5) + hash) + c; /* hash * 33 + c */
}
return hash;
}This is a hash function for strings, one line
hash = ((hash << 5) + hash) + c; /* hash * 33 + c */Is the problem, for a longer string, the hash variable will continue to become larger, and even overflow.
Thus every attempt variable is calculated once, for a large prime number do a modulo operation, will be limited within a certain range value. Try to find runs.
But this increase will take more than additional overhead, and take the remainder of what the number should also be considered, because it would limit the hash value distribution, increase the chance of a collision. But provides a way to solve the problem before operating data structures.
Reference: